This Help topic describes how to replace the following server certificates used by the ExtremeControl engine:
- Captive Portal Server Certificate - Used for remediation and registration web pages on the ExtremeControl engine.
- Internal Communications Server Certificate - Used for communication between the engine and the ExtremeCloud IQ Site Engine server, other ExtremeControl engines, and ExtremeControl assessment servers. It is also used for the ExtremeControl administrative web pages.
- RADIUS Server Certificate - Sent to end-systems during certain forms of 802.1X authentication (EAP-TLS, PEAP, and EAP-TTLS).
| NOTE: | ExtremeCloud IQ Site Engine automatically generates alarms as the ExtremeControl Engine Internal Communications Server Certificate, the Captive Server Portal Server Certificate, the RADIUS Server Certificate, the AAA Configuration Truststore, and the ExtremeControl Engine Truststore approach their expiration date. ExtremeCloud IQ Site Engine generates a Notification alarm 30 days before expiring, a Warning alarm 7 days before expiring, and a Critical alarm when the certificate expires. |
|---|
During installation, a new, unique private server key and server certificate is generated for each server. While these provide secure communication, there can be cases where you want to update to a certificate provided from an external certificate authority, or add certificates in order to meet the requirements of external components with which ExtremeCloud IQ Site Engine must communicate. Additionally, you can use a "browser-friendly" certificate so that users don't see browser certificate warnings when they access web pages.
You need a server private key and server certificate to perform the certificate replacement. If you do not have these, this topic also includes procedures that can be used to generate them.
Some instructions in this Help topic use OpenSSL software to perform certain tasks. OpenSSL is available on the ExtremeCloud IQ Site Engine engine, the ExtremeControl engine, or can be downloaded from http://www.openssl.org. After downloading and installing OpenSSL, add the OpenSSL tool to your path using the instructions in the ExtremeCloud IQ Site Engine and ExtremeControl Secure Communication Help topic section How to Add OpenSSL to Your Path. Other software tools can be used to perform these tasks, if desired.
Instructions on:
- Certificate Requirements
- Replacing the Certificate
- Verifying the Certificate
- Generating a Server Private Key and Server Certificate
Certificate Requirements
You need the RSA or DSA server private key (in PKCS #8 format) that was used to generate the server certificate. For "browser-friendly" certificates, the server certificate should identify the ExtremeControl engine by its fully qualified host name. If you do not have the server private key and server certificate, refer to the instructions for generating them.
| NOTE: | Elliptical Curve (EC) and ED25519 private key formats are not supported. |
|---|
If your certificate authority (CA) provides additional intermediate certificates, you need to provide those as well. The intermediate certificates can be used in whatever format the CA provides them. They can be in individual files, in a bundle file, or even in the same file as the server certificate.
| NOTE: | if you need to convert your key file to a PKCS #8 format, use the following OpenSSL command where <server.key> is the original non‑PKCS #8 formatted key file. (OpenSSL is available on ExtremeCloud IQ Site Engine and ExtremeControl engines. The server.key file can be copied and converted on either engine.) openssl pkcs8 -provider default -provider legacy -topk8 -in <server.key> -out server-pkcs8.key -nocrypt |
Replacing the Certificate
The following steps assume that you have a replacement server private key and server certificate ready to use. If you do not, refer to the Generating a Server Private Key and Server Certificate section below. Be aware that the replacement operation stops communication on the server's secure ports for a small period of time (about 15 seconds).
| NOTE: | If the Captive Portal server certificate identifies the engine by a fully qualified host name, be sure the captive portal is
configured with the Use Fully Qualified Domain Name option enabled in the Edit
Captive Portal window,
Network Settings tab.
Verify that end users are routed to the captive portal with the engine's
fully qualified host name (the same name used on the certificate) instead of IP address in the portal
URL and that there are no unexpected browser warnings. If the option is not enabled, then end
users can get certificate warning messages in their browsers about the wrong
server name. This happens because the IP address in
the URL does not match the domain name in the server certificate. |
|
|---|---|---|
| If you are updating the Internal Communications server certificate, be aware that other ExtremeCloud IQ Site Engine components can be affected by the change and stop trusting the server. ExtremeCloud IQ Site Engine clients and other servers must be configured to handle updated certificates using the client certificate trust mode and server certificate trust mode settings. Before updating the Internal Communications server certificate, be sure that the client and server trust modes are configured to trust the new certificate. For more information, see the Suite-Wide Tools Server Information Help topics Update Client Certificate Trust Mode window and Update Server Certificate Trust Mode window. |
To replace the server private key and server certificate:
- Access the Control > Access Control tab.
- Expand Engines in the left panel and select an ExtremeControl engine.
- In the right-panel, select Manage in the Certificates section. The Manage Certificates window opens.
- Select the Update Certificate button for the certificate you wish to replace. The Server Certificate window for that certificate opens.
- If you are updating the Captive Portal server certificate or the Internal Communications server certificate, select the option to provision a private key and certificate from files. For the RADIUS server certificate, go to step 4.
- In the Private Key section, provide a file containing the private key
that corresponds to the certificate. It must be encoded as a PKCS #8 file. Enter the
path name of the file or use the Browse button to navigate to the file. If the file is encrypted with a password, check the password box and
supply the password in the field.
- In the Certificate Files section, use the Add Files button to add one or more certificate files as provided by the certificate authority. This includes the server certificate, as well as any intermediate or chained certificates. You can multi-select files in the file chooser window, and the files can be added in any order.
- Select OK. You see a confirmation window listing your file information so that you can confirm that the information you have provided is correct. Select Yes to proceed with the certificate replacement. The private key and server certificate are updated in the engine configuration in the ExtremeCloud IQ Site Engine database.
- Enforce the engine to deploy the new private key and server
certificate. When enforced, the server's secure ports are offline for 15 seconds to
reload the certificate:
- Captive Portal Server Certificate - port 443.
- Internal Communications Server Certificate - port 8444. Additionally, if the Agent-Based Assessment Server Certificate is configured to use the Internal Certificate, port 8443 is offline.
If you have replaced the RADIUS Server certificate, the RADIUS server on the engine is restarted to automatically to load the new certificate.
Verifying the Certificate
When you have installed the new certificate, use the following steps to verify that the server is using the updated certificate.
Verifying the Captive Portal Server Certificate
When the new server certificate is installed and the captive portal web server has restarted, use one of the following methods to verify that the server is now using the proper server certificate.
Use a Browser
- Access the Registration Administration web page at
https://<ExtremeControl Engine FQDN>/administration. To eliminate browser warnings, verify that no browser warnings display when you access the web page. - Then, use your browser to view the certificate
used:
- Internet Explorer 7.0 or later: View > Security Report > View Certificates
- Mozilla Firefox 3.5 or later: Tools > Page Info > Security > View Certificates
Use OpenSSL
- Use OpenSSL to test the server connection
with the following command:
openssl s_client -connect <ExtremeControl Engine Name or IP address>:443 - The output from this program includes a section titled "Certificate
chain". This enumerates the certificates returned by the server.
For each certificate, the Subject and the Issuer display. With multiple
certificates, if the certificates are in the proper order, the issuer of each
certificate matches the subject of the following certificate. Here is a sample output from the program:
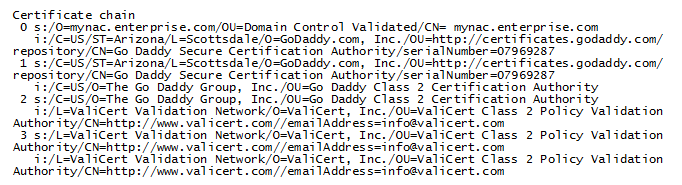
- Close the program by typing Ctrl-C.
Verifying the Internal Communications Server Certificate
When the new server certificate is installed, use one of the following methods to verify that the server is now using the proper server certificate.Use a Browser
- Access the ExtremeControl Engine Administration web page at
https://<ExtremeControl Engine FQDN>:8444/Admin/. If your intention was to eliminate browser warnings, verify that no browser warnings are displayed when you access the web page. - Then, use your browser to view the certificate
used:
- Internet Explorer 7.0 or later: Select the lock icon to the right of the URL address > View Certificates
- Microsoft Edge: Select the lock icon to the left of the URL address > Connection is secure > certificate icon
- Mozilla Firefox 3.5 or later: Select the lock icon to the left of the URL address > Connection Secure > More information > View Certificate
Use OpenSSL
- Use OpenSSL to test the server connection
with the following command:
openssl s_client -connect <ExtremeControl Engine Name or IP address>:8444 - The output from this program includes a section titled "Certificate
chain". This enumerates the certificates returned by the
server.
For each certificate, the Subject and the Issuer are displayed. With multiple
certificates, if the certificates are in the proper order, the issuer of each
certificate matches the subject of the following certificate. Here is a sample output from the program:
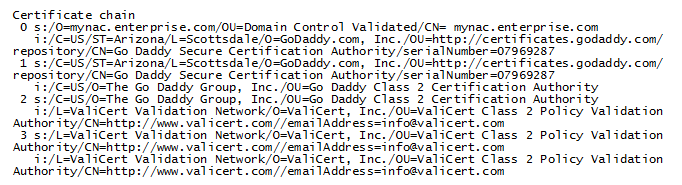
- Close the program by typing Ctrl-C.
Generating a Server Private Key and Server Certificate
If you do not have a server private key and server certificate to use as a replacement, generate them using the instructions in the linked topic in the Generating a Server Private Key and Server Certificate section.