This report provides detailed information about end-systems impacted as the result of ExtremeCloud IQ Site Engine unable to communicate with a site (Status of Down). The report also shows any events that pertain to the end-systems selected in the top table. Additionally, the report lists the risks and vulnerabilities for the device and assigns a score based on the severity of the risk.
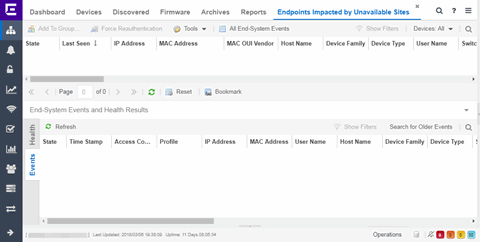
The report contains three tables:
End-System Information
The table at the top of the report lists the end-systems that are affected as the result of unavailable sites.
- State
- The end-system's connection state:
- Scan - The end-system is currently being scanned.
- Accept - The end-system is granted access with either the Accept policy or the policy returned from the RADIUS server in the filter-ID.
- Quarantine -The end-system is quarantined because the scanning test failed.
- Reject - The end-system was rejected because the assigned ExtremeControl profile was set to Reject, the MAC Locking test failed, or the RADIUS server was reachable but rejected the authentication request.
- Error - Indicates one of nine problems:
- the MAC to IP resolution failed, if assessment is enabled
- the MAC to IP resolution timed out, if assessment is enabled
- all RADIUS servers are unreachable
- the RADIUS request was non-compliant
- all assessment servers are unavailable
- the assessment server can't reach the end-system
- no assessment servers are configured
- the assessment server is not compatible with the current version of ExtremeCloud IQ Site Engine
- the username and password configured in the Assessment Server section of the Access Control options (Administration > Options > Access Control) are incorrect for the assessment server
- MAC Address
- The end-system's MAC address. MAC addresses are displayed as a full MAC address or with a MAC OUI (Organizational Unique Identifier) prefix, depending on the option you select the Access Control Options tab.
- Switch Port
- The port alias (if defined) followed by the switch port number to which the end-system is connected.
- Risk Level
- The overall risk level assigned to the end-system based on the health result of
the scan:
- Red - High Risk
- Orange - Medium Risk
- Yellow - Low Risk
- Green - No Risk
- Gray - Unknown
- Reason
- Provides additional information about the reasons why the end-system is in its particular connection state. It gives you an idea as to why a certain policy was applied to the end-system or why the end-system was rejected.
- Authentication Type
- Identifies the latest authentication method used by the end-system to connect to the network.
- State Description
- This column provides more details about the end-system state. For example, if the end-system's connection state is Reject, this column might list the RADIUS server (primary or secondary) that rejected the authentication request.
- Engine Group
- Displays what Engine group the ExtremeControl engine was in when the end-system event was generated. For example, if the Engine was in Engine group A when an end-system connected, but then later the Engine was moved to Engine group B, this column still list Engine group A for that end-system's entry.
- RFC 3580 VLAN ID
- For end-systems connected to RFC 3580-enabled switches, this is the RFC3580 VLAN ID assigned to the end-system.
- Last Quarantined
- The last date and time the end-system was quarantined. This column is hidden by default.
- Score
- The total sum of the scores for all the health details that were included as part of the quarantine decision.
- Actual
- The actual score is what the total score would be if all the health details including those marked Informational and Warning were included in the score.
- All Authentication Types
- This column displays all the authentication methods the end-system has used to authenticate.
- Last Scan Result State
- The last scan result assigned to the end-system: Scan, Accept, Quarantine, Reject, Error. This is the state that was assigned to the end-system as a result of the last completed scan. This will typically match the end-system State if scanning is currently enabled and has been performed recently.
- NAP Capable
- Indicates whether the end-system is Microsoft NAP (Network Access Protection) capable: Yes or No
- Custom 1-4
- Use these column to add additional information you want to display. You can add information for up to four Custom columns.
- Registered Email
- The registered email address supplied by the end user during the registration process.
- Registered Phone
- The registered phone number supplied by the end user during the registration process.
- Sponsor
- The registered user's sponsor, if sponsorship is enabled.
- Registration 1-5
- The text from the Custom 1-5 registration fields supplied by the end user during the registration process.
- Registration Description
- The device description supplied by the end user during the registration process.
- Groups
- End-system groups are rule components that allow you to group together devices having similar network access requirements or restrictions.
- Zone
- This field only displays if you have displayed the Zone column in the Access Control Configuration Rules table. Select the end-system zone assigned to any end-system matching this rule. See End-System Zones for more information.
- Request Attributes
- Displays the RADIUS attributes injected when the end-system requested authentication.
- Source
- Displays the origin of the event:
-
- Access Controlengine — An Access Controlengine.
- Wireless Manager — An ExtremeWireless Controller or AP.
- ExtremeXOS/Switch Engine ID Manager — An Extreme switch running ExtremeXOS/Switch Engine with the Identify Manager feature configured to send events to ExtremeCloud IQ Site Engine.
- OneFabric Connect — An ExtremeConnect module (e.g. Solutions Architecture and Innovation (SAI) integration)
- One Controller — The Extreme SDN Controller.
- TLS Client Certificate Expiration
- Expiration date of the TLS Client Certificate issued for 802.1x authentication.
- TLS Client Certificate Issuer
- Name of the issuer of the TLS Client Certificate issued for 802.1x authentication.
Events Log
The Events table displays end-system events related to the unavailability of the site.
- State
- The end-system's connection state:
- Scan - The end-system is currently being scanned.
- Accept - The end-system is granted access with either the Accept policy or the policy returned from the RADIUS server in the filter-ID.
- Quarantine -The end-system is quarantined because the scanning test failed.
- Reject - The end-system was rejected because the assigned ExtremeControl profile was set to Reject, the MAC Locking test failed, or the RADIUS server was reachable but rejected the authentication request.
- Error - Indicates one of nine problems:
- the MAC to IP resolution failed, if assessment is enabled
- the MAC to IP resolution timed out, if assessment is enabled
- all RADIUS servers are unreachable
- the RADIUS request was non-compliant
- all assessment servers are unavailable
- the assessment server can't reach the end-system
- no assessment servers are configured
- the assessment server is not compatible with the current version of NAC Manager
- the username and password configured in the Assessment Server section of the Access Control options (Administration > Options > Assessment Server) are incorrect for the assessment server
- MAC Address
- The end-system's MAC address. MAC addresses are displayed as a full MAC address or with a MAC OUI (Organizational Unique Identifier) prefix, depending on the option you have selected in the Display section of the Access Control Options (Administration > Options > Access Control).
- State Description
- This column provides more details about the end-system's state. For example, if the end-system's connection state is Reject, this column might list the RADIUS server (primary or secondary) that rejected the authentication request.
- Reason
- Provides additional information about the reasons why the end-system is in its particular connection state. It gives you an idea as to why a certain policy was applied to the end-system or why the end-system was rejected.
- Authorization
- The attributes returned by the RADIUS server for this end-system. If the end-system is connected to a switch that supports multi-authentication, then this column may not reflect the actual active policy for the authenticated user. For Layer 3 Access Control Controller engines, this column displays the policy assigned to the end-system for its authorization.
- Auth Type
- Identifies the authentication method used by the end-system to connect to the network. For Layer 3 Access Control Controller engines, this column shows IP.
- Switch IP
- The IP address of the switch to which the end-system connected. If the end-system is connected to an Access Control Controller engine, this is the Access Control Controller PEP (Policy Enforcement Point) IP address..
- Switch Location
- The physical location of the switch to which the end-system connected. If the end-system is connected to an Access Control Controller engine, this is the Access Control Controller PEP (Policy Enforcement Point) location.
- Zone
- Displays the end-system zone to which the end-system is assigned.
- Event Source
-
- Access Control Engine — A Access Control engine.
- Wireless Manager — An ExtremeWireless Wireless Controller or AP.
- ExtremeXOS/Switch Engine ID Manager — An Extreme switch running ExtremeXOS/Switch Engine with the Identify Manager feature configured to send events to ExtremeCloud IQ Site Engine.
- OneFabric Connect — A custom project (e.g. Solutions Architecture and Innovation (SAI) integration)
- One Controller — The Extreme SDN Controller.
Displays the origin of the event:
Health Log
This tab provides summary information on health results (assessment results) obtained for the end-system selected in the table above. You can specify the number of health result summaries displayed using the Health Result Persistence options in the Data Persistence Options.
- Risk
- The risk level assigned to the end-system based on the health result of the scan: High Risk, Medium Risk, Low Risk, or No Risk.
- Score
- The score assigned to the test case. The score is a value between 0.0 and 10.0. In the case of agent-based test cases, the score is either 0.0 for a passed test, or 10.0 for a failed test, unless specifically overwritten by the scoring override configuration.
- Scoring Mode
- The scoring mode that was used at the time the test was performed.
- Applied — The score returned by this test was included as part of the quarantine decision.
- Informational — The score returned by this test was reported, but did not apply toward a quarantine decision.
- Warning — The score returned by this test was only used to provide end user assessment warnings via the Notification portal web page.
- CVE IDs
- The CVE (Common Vulnerability and Exposures) ID assigned to the security vulnerability or exposure. For more information on CVE IDs, refer to the following URL: https://cve.mitre.org/.
- Assessment
- The list of test sets that were run during assessment, for example, Default Nessus, Default Agent-less, and Default Agent-based. Test sets are defined as part of the assessment configuration. If the end-system is NAP capable, then this column displays Microsoft NAP indicating that NAP performed the assessment.
- Remediation
- For agent-based assessment, this column lists the results of remediation attempts: Success, Failed, or Not Attempted.
- Type
- A "type" is assigned to each security risk found on a port
during an assessment, and is used to determine whether to Quarantine an end-system.
Types are configurable on the assessment agent.
There are three types:
- Hole — The port is vulnerable to attack.
- Warning — The port may be vulnerable to attack.
- Note — There may be a security risk on the port.
For information on related help topics: