ExtremeCloud IQ Site Engine
26.02.13 Release Notes
A PDF copy of these release notes can be found here.
ExtremeCloud IQ Site Engine includes all the features and functionality of Extreme Management Center as well as issues that have been resolved and configuration changes for this release.
If you are an existing Extreme Management Center customer, contact your representative to have your Extreme Management Center license migrated to an ExtremeCloud IQ Site Engine license. The ExtremeCloud IQ Site Engine license also includes licensing for ExtremeAnalytics.
| IMPORTANT: |
|
For information regarding the features supported by specific devices, see the Firmware Support Matrix. Version 26.02.13 of ExtremeCloud IQ Site Engine supports the devices listed in the matrix.
Devices that do not have serial numbers or MAC addresses in Extreme Management Center must be rediscovered after you upgrade to ExtremeCloud IQ Site Engine before they can be onboarded to ExtremeCloud IQ.
Connected mode only - If your number of devices exceeds your licenses available, ExtremeCloud IQ Site Engine transitions to a license violation state and your access to ExtremeCloud IQ Site Engine is locked. To resolve the license shortage you need to access the Extreme Networks portal or ExtremeCloud IQ to evaluate the quantities of available Pilot and Navigator licenses versus the number of licenses required by ExtremeCloud IQ Site Engine.
Licensing Changes
The following sections describe licensing changes in ExtremeCloud IQ Site Engine software releases.
Version 25.05.10
Starting in ExtremeCloud IQ Site Engine version 25.05.10 the new Extreme Platform ONE subscriptions are compatible with ExtremeCloud IQ Site Engine in air gap deployments.
Version 25.02.10
Starting in ExtremeCloud IQ Site Engine version 25.02.10 the new Extreme Platform ONE subscriptions are recognized if ExtremeCloud IQ Site Engine is onboarded to ExtremeCloud IQ or Extreme Platform ONE.
Version 23.02.10
Starting in ExtremeCloud IQ Site Engine version 23.02.10 each stack member consumes a license in connected mode. In connected mode, ExtremeCloud IQ Site Engine now reports stack members to ExtremeCloud IQ. If you use stacks in connected mode, ensure that enough ExtremeCloud IQ Pilot licenses are in the license pool before upgrading to ExtremeCloud IQ Site Engine 23.02.10 or later.
Version 21.09.10
For users upgrading from Extreme Management Center to ExtremeCloud IQ Site Engine, note that the XIQ-NAC subscription must be used instead of IA-ES- license. For new users that complete an initial install of ExtremeCloud IQ Site Engine, ExtremeControl licensing does not include end-system capabilities.
Version 21.04.10
Starting in ExtremeCloud IQ Site Engine version 21.04.10, your ExtremeAnalytics license is included as part of your ExtremeCloud IQ Pilot license. Separate licenses are no longer required.
End of Software Maintenance
In ExtremeCloud IQ Site Engine version 24.10.12 and after, the following components and features are deprecated and removed:
-
Microsoft Azure Connect module (for multi-cloud integration)
-
Ekahau map import
In ExtremeCloud IQ Site Engine version 24.07.10 and after, the following components and features are deprecated and removed:
-
ExtremeCompliance, also known as Information Governance Engine
-
Public Cloud Dashboard
The following components and features reached end-of-software-maintenance on 30th September 2023:
-
Guest and IoT Manager - last version is 23.07.11.6 (not compatible with ExtremeCloud IQ Site Engine version 24.07.10 and after)
-
Fabric Manager - last version is 22.09.13.5
-
Posture Assessment (both the agent-based and agent-less)
The mobile application "ExtremeManagement ZTP+" was removed from the Google Play store in August 2024.
Onboarding ExtremeCloud IQ Site Engine to ExtremeCloud IQ in Connected Deployment Mode
After installing or upgrading to ExtremeCloud IQ Site Engine, you need to onboard ExtremeCloud IQ Site Engine to ExtremeCloud IQ. When the onboarding is complete, you can then access ExtremeCloud IQ Site Engine.
Entering your ExtremeCloud IQ name and password are required during the first-time login to ExtremeCloud IQ Site Engine.
| NOTE: | If Extreme Management Center is onboarded to ExtremeCloud IQ, when you upgrade to ExtremeCloud IQ Site Engine, you need to remove Extreme Management Center from ExtremeCloud IQ before onboarding ExtremeCloud IQ Site Engine. |
Enhancements
The following enhancements were made to ExtremeCloud IQ Site Engine in this release. For additional information about each of the enhancements listed in the release notes, see ExtremeCloud IQ Site Engine Documentation .
Customer Found Defects and Known Issues
Customer Found Defects Addressed 26.02.13
| ExtremeControl CFDs Addressed | ID |
|---|---|
| Addressed an issue with the End-System Events Report download URL failing for GUI users with @ symbol in username. | 03268435 CFD-17110 |
| Addressed an issue with the End-System Events export option to unselect "Use Table Filters" causes a specific MAC export to show the entire FS/FSE table for all MAC addresses available. | 03268435 CFD-17093 |
|
ExtremeManagement CFDs Addressed |
ID |
|---|---|
| Addressed an issue where device polling stops during automatic garbage cleanup. Now resolved in this release with updated garbage clean logic to G1GC. | 02868328 03264286 CFD-16511 |
| Addressed an issue where the browser would send incorrect session cookies to Connect, and the server would resolve to an application session that Connect neither owned or recognized. The issue caused Connect to produce an Internal Server Error message in the browser and prevent the user from configuring Connect. | 03264957 CFD-17029 |
| Addressed an issue where Fabric Engine ports configured with Switched UNI port template were not added to the L2-VSN after performing "Read Device" action. A validation check has been added to require L2-VSN service name to match with the UNI type service name. | 03224806 CFD-16693 |
Customer Found Defects Addressed 26.02.12
| ExtremeCloud IQ Site Engine CFDs Addressed | ID |
|---|---|
|
Addressed issue with web terminal not functioning correctly in Firefox version 148. |
03246196 03246860 03244863 CFD-16597 |
| Addressed an issue with Linux OS upgrade information in documentation. Text updated for additional context regarding Linux OS upgrade and version accuracy. | 03251779 CFD-16856 |
|
ExtremeManagement CFDs Addressed |
ID |
|---|---|
|
Addressed an issue with the web server not terminating a session after the default or configured timeout expiry. |
03144603 CFD-14791 |
| Addressed an issue with Switch VLAN IP addresses being removed when making changes related to VRRP settings in VLAN Service Definitions. |
03226827 |
| Addressed an issue where custom variables for a site could appear as a global variable. | 03221736 CFD-16365 |
| Addressed an issue where SSH access was being enabled on all Virtual Routers. Adjusted script that enables Cloud Connector to enable SSH only on necessary Virtual Router. | 03250144 CFD-16674 |
| Addressed an issue with GUI performance degradation occurring approximately two weeks after upgrades. | 03089186 CFD-16098 |
| Addressed an issue with an enforce errors. Corrected the vendor profiles settings for default and max VRFs for Fabric Engine 5320 series. Resolved enforce issue with Fabric Engine 4220 and 5320 failing due to treating VRF-Mgmt as lowercase. | 03209595 CFD-15890 |
Customer Found Defects Addressed 26.02.11
| ExtremeControl CFDs Addressed | ID |
|---|---|
| Addressed an issue with Registered Username vs Username from Certificate. Improved the RADIUS Accounting logic properly not to update the Username when Override Username by Registered User option is enabled. | CFD-16311 |
| ExtremeManagement CFDs Addressed | ID |
|---|---|
| Addressed an issue with Connect Palo-Alto module causing server performance issues over time. This issue was resolved in version 26.02.10, now a blocking queue to decouple event production from consumption, eliminating the bottleneck of the original single-threaded, lock-heavy design. A small executor is used to send messages concurrently, enabling efficient batching of user-ID updates. | 02959822 CFD-13071 |
Customer Found Defects Addressed 26.02.10
| ExtremeAnalytics CFDs Addressed | ID |
|---|---|
| Addressed an issue with missing response time values for some flows. Now added a diagnostic monitor in the flow collector to determine when packets and flows drop due to insufficient resources. | 03143806 CFD-14775 |
| ExtremeControl CFDs Addressed | ID |
|---|---|
| Addressed an issue when a redirect URL is configured to HTTP, the redirection was not working properly in some cases. | 03140932 CFD-15096 |
| Addressed an issue where the Entra ID connectivity test returned a success message even when the token endpoint was configured incorrectly. | 03177648 CFD-15298 |
| Addressed an issue with the RFC3580 column in End-Systems table. Now displaying the RFC3580 value properly. | 03192819 CFD-15557 |
| Addressed an issue with the 4 GB NAC process memory RAM limit. Now increased the NAC process memory to 6 GB for systems with 16 GB or more RAM, and 8 GB for systems with 24 GB or more RAM. | 03185348 CFD-15653 |
| Addressed an issue with being unable to change the MAC user password for an EXOS device. Now working to a device with firmware 33.5.0.270 but issue is present on a device with firmware version 33.5.2.116. EXOS device firmware changes are required to fix. | 03193272 CFD-15688 |
| Addressed an issue with CRL disappearing from Update AAA Trusted Certificate Authorities area if you start to edit the text field for a CRL from the lower table and click cancel. Now the CRL list remains in this scenario. | 03223503 CFD-16025 |
| Addressed an issue of ExtremeControl unable to apply to RADIUS packets after a restart or enforce if a significant number of switches are SNMP unreachable. Now improved the Access Control Engine scalability by adding adjustable pool and queue size in Engine settings. Increased java memory. Added a configurable option for port information in SNMP. Enhanced the SNMP synchronization logic in Access Control. | 03155396 03139197 CFD-14883 |
| Addressed an issue where diagnostics for switch configuration did not show a failure to connect to CLI. Added error handling to the switch configuration process. Previously, the switch configuration process could report successful completion even when it was terminated early due to an uncaught exception, and the RADIUS configurations were not attempted. This fix avoids that false-positive scenario. | 03095202 CFD-14796 |
| ExtremeManagement CFDs Addressed | ID |
|---|---|
| Addressed an issue with the Connect Palo-Alto module causing server performance issues over time. Now a blocking queue to decouple event production from consumption, eliminating the bottleneck of the original single-threaded, lock-heavy design. A small executor sends messages concurrently, enabling efficient batching of user-ID updates. |
02959822 |
| Addressed an issue where Enable Trap Refresh ran for all devices at same time overloading resources. Now running the Trap Refresh script in a batch size of 50 in a multi-threaded environment. | 03102202 CFD-14037 |
| Addressed an issue with the device list auto refreshing every 30 seconds which resets multiple device selections to only the first device. Now selected devices will stay selected until changed manually. | 03211180 CFD-15837 |
| Addressed an issue with a Validator EL Interpolation Code Injection vulnerability. Updated hibernate-validator and hibernate-validator-cdi to version 6.2.0 to address security vulnerabilites CVE-2025-35036, CVE-2020-5245, CVE-2025-4428. | 03187903 CFD-15530 |
| Addressed an issue with CPU usage spiking while loop failed to terminate because a normalized IPv6 address was being compared to a compressed IPv6 address. | 03146761 CFD-15136 |
| Addressed an issue with the ping only status poll in IPv6 interfaces showing as offline. Found and fixed the coding for the nspingd service to support the IPv6 ping feature. | 03172751 CFD-15137 |
| Addressed an issue where a non-admin user could get SNMP credential definitions. | 03220122 CFD-15956 |
Known Issues Addressed in 26.02.12
| Addressed an issue with Extreme Networks 8730-32D devices incorrectly using a Navigator subscription. |
Known Issues Addressed in 26.02.11
| Addressed an issue where 5420M-16MW-32P-4YE was not consuming a correct subscription tier in Connected mode. |
| Addressed an issue where a non-admin user could get CLI credential definitions. |
| Addressed an issue where an incorrect picture for AP5060U and AP5060D appeared on the map. |
| Addressed an issue where the 6Ghz radio was missing from the context menu for AP5060U and AP5060D. |
| Addressed an issue with some widgets appearing as disabled in Network > Dashboard > Impact Analysis > Network and Application Performance. |
Known Issues Addressed in 26.02.10
| Addressed a vulnerability that could expose user credentials stored in the local password repository to the admin. |
| Addressed an issue with high CPU utilization from the MuObserverMgr process. |
Addressed Vulnerabilities
This section presents the vulnerabilities reported by vulnerability scanners in previous versions. The following components received updates in 26.02 regardless of whether the vulnerability could have been exploited or not. If you need more information on vulnerability testing, see Security and Vulnerability Testing.
26.02.13 ExtremeAnalytics, and Application Analytics Traffic Sensor images:
CVE-2026-31431, CVE-2026-34500, CVE-2026-34487, CVE-2026-34486, CVE-2026-34483, CVE-2019-19221, CVE-2023-52890, CVE-2023-53421, CVE-2023-53520, CVE-2023-53662, CVE-2023-54207, CVE-2024-20696, CVE-2025-25724, CVE-2025-37849, CVE-2025-38057, CVE-2025-38125, CVE-2025-38232, CVE-2025-38408, CVE-2025-38591, CVE-2025-40149, CVE-2025-40164, CVE-2025-5914, CVE-2025-5916, CVE-2025-5917, CVE-2025-5918, CVE-2025-60753, CVE-2025-68211, CVE-2025-68340, CVE-2025-68365, CVE-2025-68725, CVE-2025-68817, CVE-2025-71162, CVE-2025-71163, CVE-2025-71185, CVE-2025-71186, CVE-2025-71188, CVE-2025-71190, CVE-2025-71191, CVE-2025-71194, CVE-2025-71196, CVE-2025-71197, CVE-2025-71199, CVE-2025-7519, CVE-2026-22007, CVE-2026-22013, CVE-2026-22016, CVE-2026-22018, CVE-2026-22021, CVE-2026-22997, CVE-2026-22998, CVE-2026-22999, CVE-2026-23001, CVE-2026-23003, CVE-2026-23011, CVE-2026-23026, CVE-2026-23033, CVE-2026-23037, CVE-2026-23038, CVE-2026-23049, CVE-2026-23056, CVE-2026-23058, CVE-2026-23060, CVE-2026-23061, CVE-2026-23063, CVE-2026-23064, CVE-2026-23071, CVE-2026-23073, CVE-2026-23074, CVE-2026-23075, CVE-2026-23076, CVE-2026-23078, CVE-2026-23080, CVE-2026-23083, CVE-2026-23084, CVE-2026-23085, CVE-2026-23087, CVE-2026-23089, CVE-2026-23090, CVE-2026-23091, CVE-2026-23093, CVE-2026-23095, CVE-2026-23096, CVE-2026-23097, CVE-2026-23098, CVE-2026-23099, CVE-2026-23101, CVE-2026-23103, CVE-2026-23105, CVE-2026-23108, CVE-2026-23111, CVE-2026-23119, CVE-2026-23120, CVE-2026-23121, CVE-2026-23124, CVE-2026-23125, CVE-2026-23128, CVE-2026-23133, CVE-2026-23145, CVE-2026-23146, CVE-2026-23150, CVE-2026-23164, CVE-2026-23167, CVE-2026-23170, CVE-2026-23209, CVE-2026-23865, CVE-2026-2673, CVE-2026-28387, CVE-2026-28388, CVE-2026-28389, CVE-2026-28390, CVE-2026-31789, CVE-2026-31790, CVE-2026-32249, CVE-2026-32597, CVE-2026-33412, CVE-2026-34268, CVE-2026-34982, CVE-2026-35177, CVE-2026-35385, CVE-2026-35386, CVE-2026-35387, CVE-2026-35388, CVE-2026-35414, CVE-2026-3731, CVE-2026-39881, CVE-2026-40706, CVE-2026-4111, CVE-2026-4878, CVE-2026-4897
26.02.13 ExtremeControl images:
CVE-2026-31431, CVE-2025-61594, CVE-2026-34500, CVE-2026-34487, CVE-2026-34486, CVE-2026-34483, CVE-2019-19221, CVE-2023-52890, CVE-2023-53421, CVE-2023-53520, CVE-2023-53662, CVE-2023-54207, CVE-2024-20696, CVE-2025-25724, CVE-2025-37849, CVE-2025-38057, CVE-2025-38125, CVE-2025-38232, CVE-2025-38408, CVE-2025-38591, CVE-2025-40149, CVE-2025-40164, CVE-2025-5914, CVE-2025-5916, CVE-2025-5917, CVE-2025-5918, CVE-2025-60753, CVE-2025-68211, CVE-2025-68340, CVE-2025-68365, CVE-2025-68725, CVE-2025-68817, CVE-2025-71162, CVE-2025-71163, CVE-2025-71185, CVE-2025-71186, CVE-2025-71188, CVE-2025-71190, CVE-2025-71191, CVE-2025-71194, CVE-2025-71196, CVE-2025-71197, CVE-2025-71199, CVE-2025-7519, CVE-2026-22007, CVE-2026-22013, CVE-2026-22016, CVE-2026-22018, CVE-2026-22021, CVE-2026-22997, CVE-2026-22998, CVE-2026-22999, CVE-2026-23001, CVE-2026-23003, CVE-2026-23011, CVE-2026-23026, CVE-2026-23033, CVE-2026-23037, CVE-2026-23038, CVE-2026-23049, CVE-2026-23056, CVE-2026-23058, CVE-2026-23060, CVE-2026-23061, CVE-2026-23063, CVE-2026-23064, CVE-2026-23071, CVE-2026-23073, CVE-2026-23074, CVE-2026-23075, CVE-2026-23076, CVE-2026-23078, CVE-2026-23080, CVE-2026-23083, CVE-2026-23084, CVE-2026-23085, CVE-2026-23087, CVE-2026-23089, CVE-2026-23090, CVE-2026-23091, CVE-2026-23093, CVE-2026-23095, CVE-2026-23096, CVE-2026-23097, CVE-2026-23098, CVE-2026-23099, CVE-2026-23101, CVE-2026-23103, CVE-2026-23105, CVE-2026-23108, CVE-2026-23111, CVE-2026-23119, CVE-2026-23120, CVE-2026-23121, CVE-2026-23124, CVE-2026-23125, CVE-2026-23128, CVE-2026-23133, CVE-2026-23145, CVE-2026-23146, CVE-2026-23150, CVE-2026-23164, CVE-2026-23167, CVE-2026-23170, CVE-2026-23209, CVE-2026-23865, CVE-2026-2673, CVE-2026-28387, CVE-2026-28388, CVE-2026-28389, CVE-2026-28390, CVE-2026-31789, CVE-2026-31790, CVE-2026-32249, CVE-2026-32597, CVE-2026-33412, CVE-2026-34268, CVE-2026-34982, CVE-2026-35177, CVE-2026-35385, CVE-2026-35386, CVE-2026-35387, CVE-2026-35388, CVE-2026-35414, CVE-2026-3731, CVE-2026-39881, CVE-2026-40706, CVE-2026-4111, CVE-2026-4878, CVE-2026-4897
26.02.13 ExtremeCloud IQ Site Engine images:
CVE-2026-31431, CVE-2019-19221, CVE-2023-52890, CVE-2023-53421, CVE-2023-53520, CVE-2023-53662, CVE-2023-54207, CVE-2024-20696, CVE-2025-25724, CVE-2025-37849, CVE-2025-38057, CVE-2025-38125, CVE-2025-38232, CVE-2025-38408, CVE-2025-38591, CVE-2025-40149, CVE-2025-40164, CVE-2025-5914, CVE-2025-5916, CVE-2025-5917, CVE-2025-5918, CVE-2025-60753, CVE-2025-68211, CVE-2025-68340, CVE-2025-68365, CVE-2025-68725, CVE-2025-68817, CVE-2025-71162, CVE-2025-71163, CVE-2025-71185, CVE-2025-71186, CVE-2025-71188, CVE-2025-71190, CVE-2025-71191, CVE-2025-71194, CVE-2025-71196, CVE-2025-71197, CVE-2025-71199, CVE-2025-7519, CVE-2026-22007, CVE-2026-22013, CVE-2026-22016, CVE-2026-22018, CVE-2026-22021, CVE-2026-22997, CVE-2026-22998, CVE-2026-22999, CVE-2026-23001, CVE-2026-23003, CVE-2026-23011, CVE-2026-23026, CVE-2026-23033, CVE-2026-23037, CVE-2026-23038, CVE-2026-23049, CVE-2026-23056, CVE-2026-23058, CVE-2026-23060, CVE-2026-23061, CVE-2026-23063, CVE-2026-23064, CVE-2026-23071, CVE-2026-23073, CVE-2026-23074, CVE-2026-23075, CVE-2026-23076, CVE-2026-23078, CVE-2026-23080, CVE-2026-23083, CVE-2026-23084, CVE-2026-23085, CVE-2026-23087, CVE-2026-23089, CVE-2026-23090, CVE-2026-23091, CVE-2026-23093, CVE-2026-23095, CVE-2026-23096, CVE-2026-23097, CVE-2026-23098, CVE-2026-23099, CVE-2026-23101, CVE-2026-23103, CVE-2026-23105, CVE-2026-23108, CVE-2026-23111, CVE-2026-23119, CVE-2026-23120, CVE-2026-23121, CVE-2026-23124, CVE-2026-23125, CVE-2026-23128, CVE-2026-23133, CVE-2026-23145, CVE-2026-23146, CVE-2026-23150, CVE-2026-23164, CVE-2026-23167, CVE-2026-23170, CVE-2026-23209, CVE-2026-23865, CVE-2026-2673, CVE-2026-28387, CVE-2026-28388, CVE-2026-28389, CVE-2026-28390, CVE-2026-31789, CVE-2026-31790, CVE-2026-32249, CVE-2026-32597, CVE-2026-33412, CVE-2026-34268, CVE-2026-34982, CVE-2026-35177, CVE-2026-35385, CVE-2026-35386, CVE-2026-35387, CVE-2026-35388, CVE-2026-35414, CVE-2026-3731, CVE-2026-39881, CVE-2026-40706, CVE-2026-4111, CVE-2026-4878, CVE-2026-4897
26.02.12 ExtremeAnalytics, and Application Analytics Traffic Sensor images:
CVE-2026-24734, CVE-2026-24733, CVE-2025-66614, CVE-2022-49465, CVE-2024-36903, CVE-2024-36927, CVE-2024-37354, CVE-2024-41014, CVE-2024-46830, CVE-2024-47666, CVE-2024-49968, CVE-2025-0167, CVE-2025-15366, CVE-2025-15367, CVE-2025-22022, CVE-2025-22111, CVE-2025-22121, CVE-2025-31648, CVE-2025-38022, CVE-2025-38129, CVE-2025-38556, CVE-2025-40040, CVE-2025-40083, CVE-2025-40110, CVE-2025-40211, CVE-2025-40248, CVE-2025-40252, CVE-2025-40253, CVE-2025-40254, CVE-2025-40257, CVE-2025-40258, CVE-2025-40259, CVE-2025-40261, CVE-2025-40262, CVE-2025-40263, CVE-2025-40264, CVE-2025-40269, CVE-2025-40271, CVE-2025-40272, CVE-2025-40273, CVE-2025-40275, CVE-2025-40277, CVE-2025-40278, CVE-2025-40279, CVE-2025-40280, CVE-2025-40281, CVE-2025-40282, CVE-2025-40283, CVE-2025-40304, CVE-2025-40306, CVE-2025-40308, CVE-2025-40309, CVE-2025-40312, CVE-2025-40313, CVE-2025-40314, CVE-2025-40315, CVE-2025-40317, CVE-2025-40319, CVE-2025-40321, CVE-2025-40322, CVE-2025-40324, CVE-2025-40331, CVE-2025-40342, CVE-2025-40343, CVE-2025-40345, CVE-2025-40360, CVE-2025-40363, CVE-2025-61984, CVE-2025-61985, CVE-2025-68161, CVE-2025-68168, CVE-2025-68176, CVE-2025-68177, CVE-2025-68185, CVE-2025-68191, CVE-2025-68192, CVE-2025-68194, CVE-2025-68200, CVE-2025-68204, CVE-2025-68217, CVE-2025-68220, CVE-2025-68227, CVE-2025-68229, CVE-2025-68238, CVE-2025-68241, CVE-2025-68244, CVE-2025-68245, CVE-2025-68254, CVE-2025-68255, CVE-2025-68257, CVE-2025-68258, CVE-2025-68261, CVE-2025-68264, CVE-2025-68266, CVE-2025-68282, CVE-2025-68284, CVE-2025-68285, CVE-2025-68286, CVE-2025-68287, CVE-2025-68288, CVE-2025-68289, CVE-2025-68290, CVE-2025-68295, CVE-2025-68301, CVE-2025-68302, CVE-2025-68303, CVE-2025-68308, CVE-2025-68312, CVE-2025-68321, CVE-2025-68325, CVE-2025-68327, CVE-2025-68328, CVE-2025-68330, CVE-2025-68331, CVE-2025-68332, CVE-2025-68335, CVE-2025-68336, CVE-2025-68337, CVE-2025-68339, CVE-2025-68344, CVE-2025-68346, CVE-2025-68349, CVE-2025-68354, CVE-2025-68362, CVE-2025-68364, CVE-2025-68366, CVE-2025-68367, CVE-2025-68372, CVE-2025-68724, CVE-2025-68727, CVE-2025-68728, CVE-2025-68732, CVE-2025-68733, CVE-2025-68734, CVE-2025-68740, CVE-2025-68746, CVE-2025-68757, CVE-2025-68758, CVE-2025-68759, CVE-2025-68764, CVE-2025-68765, CVE-2025-68767, CVE-2025-68769, CVE-2025-68771, CVE-2025-68774, CVE-2025-68776, CVE-2025-68777, CVE-2025-68780, CVE-2025-68782, CVE-2025-68783, CVE-2025-68785, CVE-2025-68787, CVE-2025-68788, CVE-2025-68795, CVE-2025-68796, CVE-2025-68797, CVE-2025-68799, CVE-2025-68800, CVE-2025-68801, CVE-2025-68803, CVE-2025-68804, CVE-2025-68808, CVE-2025-68813, CVE-2025-68814, CVE-2025-68815, CVE-2025-68816, CVE-2025-68818, CVE-2025-68819, CVE-2025-68820, CVE-2025-68821, CVE-2025-71064, CVE-2025-71066, CVE-2025-71068, CVE-2025-71069, CVE-2025-71075, CVE-2025-71077, CVE-2025-71078, CVE-2025-71079, CVE-2025-71081, CVE-2025-71082, CVE-2025-71083, CVE-2025-71084, CVE-2025-71085, CVE-2025-71086, CVE-2025-71087, CVE-2025-71091, CVE-2025-71093, CVE-2025-71094, CVE-2025-71096, CVE-2025-71097, CVE-2025-71098, CVE-2025-71102, CVE-2025-71104, CVE-2025-71105, CVE-2025-71108, CVE-2025-71111, CVE-2025-71112, CVE-2025-71113, CVE-2025-71114, CVE-2025-71116, CVE-2025-71118, CVE-2025-71120, CVE-2025-71121, CVE-2025-71125, CVE-2025-71127, CVE-2025-71131, CVE-2025-71132, CVE-2025-71133, CVE-2025-71136, CVE-2025-71137, CVE-2025-71147, CVE-2025-71154, CVE-2025-71180, CVE-2025-71182, CVE-2026-0865, CVE-2026-1519, CVE-2026-1965, CVE-2026-22976, CVE-2026-22977, CVE-2026-22978, CVE-2026-22980, CVE-2026-22982, CVE-2026-22984, CVE-2026-22990, CVE-2026-22991, CVE-2026-22992, CVE-2026-23019, CVE-2026-23020, CVE-2026-23021, CVE-2026-23047, CVE-2026-23268, CVE-2026-23269, CVE-2026-25749, CVE-2026-26007, CVE-2026-26269, CVE-2026-27448, CVE-2026-27459, CVE-2026-2781, CVE-2026-28417, CVE-2026-28418, CVE-2026-28419, CVE-2026-28420, CVE-2026-28421, CVE-2026-28422, CVE-2026-29111, CVE-2026-30922, CVE-2026-3104, CVE-2026-3119, CVE-2026-3497, CVE-2026-3591, CVE-2026-3731, CVE-2026-3783, CVE-2026-3784, CVE-2026-3805
26.02.12 ExtremeControl images:
CVE-2026-24734, CVE-2026-24733, CVE-2025-66614, CVE-2026-2003, CVE-2026-2004, CVE-2026-2005, CVE-2026-2006, CVE-2022-49465, CVE-2024-36903, CVE-2024-36927, CVE-2024-37354, CVE-2024-41014, CVE-2024-46830, CVE-2024-47666, CVE-2024-49968, CVE-2025-0167, CVE-2025-15366, CVE-2025-15367, CVE-2025-22022, CVE-2025-22111, CVE-2025-22121, CVE-2025-31648, CVE-2025-38022, CVE-2025-38129, CVE-2025-38556, CVE-2025-40040, CVE-2025-40083, CVE-2025-40110, CVE-2025-40211, CVE-2025-40248, CVE-2025-40252, CVE-2025-40253, CVE-2025-40254, CVE-2025-40257, CVE-2025-40258, CVE-2025-40259, CVE-2025-40261, CVE-2025-40262, CVE-2025-40263, CVE-2025-40264, CVE-2025-40269, CVE-2025-40271, CVE-2025-40272, CVE-2025-40273, CVE-2025-40275, CVE-2025-40277, CVE-2025-40278, CVE-2025-40279, CVE-2025-40280, CVE-2025-40281, CVE-2025-40282, CVE-2025-40283, CVE-2025-40304, CVE-2025-40306, CVE-2025-40308, CVE-2025-40309, CVE-2025-40312, CVE-2025-40313, CVE-2025-40314, CVE-2025-40315, CVE-2025-40317, CVE-2025-40319, CVE-2025-40321, CVE-2025-40322, CVE-2025-40324, CVE-2025-40331, CVE-2025-40342, CVE-2025-40343, CVE-2025-40345, CVE-2025-40360, CVE-2025-40363, CVE-2025-61984, CVE-2025-61985, CVE-2025-68161, CVE-2025-68168, CVE-2025-68176, CVE-2025-68177, CVE-2025-68185, CVE-2025-68191, CVE-2025-68192, CVE-2025-68194, CVE-2025-68200, CVE-2025-68204, CVE-2025-68217, CVE-2025-68220, CVE-2025-68227, CVE-2025-68229, CVE-2025-68238, CVE-2025-68241, CVE-2025-68244, CVE-2025-68245, CVE-2025-68254, CVE-2025-68255, CVE-2025-68257, CVE-2025-68258, CVE-2025-68261, CVE-2025-68264, CVE-2025-68266, CVE-2025-68282, CVE-2025-68284, CVE-2025-68285, CVE-2025-68286, CVE-2025-68287, CVE-2025-68288, CVE-2025-68289, CVE-2025-68290, CVE-2025-68295, CVE-2025-68301, CVE-2025-68302, CVE-2025-68303, CVE-2025-68308, CVE-2025-68312, CVE-2025-68321, CVE-2025-68325, CVE-2025-68327, CVE-2025-68328, CVE-2025-68330, CVE-2025-68331, CVE-2025-68332, CVE-2025-68335, CVE-2025-68336, CVE-2025-68337, CVE-2025-68339, CVE-2025-68344, CVE-2025-68346, CVE-2025-68349, CVE-2025-68354, CVE-2025-68362, CVE-2025-68364, CVE-2025-68366, CVE-2025-68367, CVE-2025-68372, CVE-2025-68724, CVE-2025-68727, CVE-2025-68728, CVE-2025-68732, CVE-2025-68733, CVE-2025-68734, CVE-2025-68740, CVE-2025-68746, CVE-2025-68757, CVE-2025-68758, CVE-2025-68759, CVE-2025-68764, CVE-2025-68765, CVE-2025-68767, CVE-2025-68769, CVE-2025-68771, CVE-2025-68774, CVE-2025-68776, CVE-2025-68777, CVE-2025-68780, CVE-2025-68782, CVE-2025-68783, CVE-2025-68785, CVE-2025-68787, CVE-2025-68788, CVE-2025-68795, CVE-2025-68796, CVE-2025-68797, CVE-2025-68799, CVE-2025-68800, CVE-2025-68801, CVE-2025-68803, CVE-2025-68804, CVE-2025-68808, CVE-2025-68813, CVE-2025-68814, CVE-2025-68815, CVE-2025-68816, CVE-2025-68818, CVE-2025-68819, CVE-2025-68820, CVE-2025-68821, CVE-2025-71064, CVE-2025-71066, CVE-2025-71068, CVE-2025-71069, CVE-2025-71075, CVE-2025-71077, CVE-2025-71078, CVE-2025-71079, CVE-2025-71081, CVE-2025-71082, CVE-2025-71083, CVE-2025-71084, CVE-2025-71085, CVE-2025-71086, CVE-2025-71087, CVE-2025-71091, CVE-2025-71093, CVE-2025-71094, CVE-2025-71096, CVE-2025-71097, CVE-2025-71098, CVE-2025-71102, CVE-2025-71104, CVE-2025-71105, CVE-2025-71108, CVE-2025-71111, CVE-2025-71112, CVE-2025-71113, CVE-2025-71114, CVE-2025-71116, CVE-2025-71118, CVE-2025-71120, CVE-2025-71121, CVE-2025-71125, CVE-2025-71127, CVE-2025-71131, CVE-2025-71132, CVE-2025-71133, CVE-2025-71136, CVE-2025-71137, CVE-2025-71147, CVE-2025-71154, CVE-2025-71180, CVE-2025-71182, CVE-2026-0865, CVE-2026-1519, CVE-2026-1965, CVE-2026-22976, CVE-2026-22977, CVE-2026-22978, CVE-2026-22980, CVE-2026-22982, CVE-2026-22984, CVE-2026-22990, CVE-2026-22991, CVE-2026-22992, CVE-2026-23019, CVE-2026-23020, CVE-2026-23021, CVE-2026-23047, CVE-2026-23268, CVE-2026-23269, CVE-2026-25749, CVE-2026-26007, CVE-2026-26269, CVE-2026-27448, CVE-2026-27459, CVE-2026-2781, CVE-2026-28417, CVE-2026-28418, CVE-2026-28419, CVE-2026-28420, CVE-2026-28421, CVE-2026-28422, CVE-2026-29111, CVE-2026-30922, CVE-2026-3104, CVE-2026-3119, CVE-2026-3497, CVE-2026-3591, CVE-2026-3731, CVE-2026-3783, CVE-2026-3784, CVE-2026-3805
26.02.12 ExtremeCloud IQ Site Engine images:
CVE-2026-2003, CVE-2026-2004, CVE-2026-2005, CVE-2026-2006, CVE-2022-49465, CVE-2024-36903, CVE-2024-36927, CVE-2024-37354, CVE-2024-41014, CVE-2024-46830, CVE-2024-47666, CVE-2024-49968, CVE-2025-0167, CVE-2025-15366, CVE-2025-15367, CVE-2025-22022, CVE-2025-22111, CVE-2025-22121, CVE-2025-31648, CVE-2025-38022, CVE-2025-38129, CVE-2025-38556, CVE-2025-40040, CVE-2025-40083, CVE-2025-40110, CVE-2025-40211, CVE-2025-40248, CVE-2025-40252, CVE-2025-40253, CVE-2025-40254, CVE-2025-40257, CVE-2025-40258, CVE-2025-40259, CVE-2025-40261, CVE-2025-40262, CVE-2025-40263, CVE-2025-40264, CVE-2025-40269, CVE-2025-40271, CVE-2025-40272, CVE-2025-40273, CVE-2025-40275, CVE-2025-40277, CVE-2025-40278, CVE-2025-40279, CVE-2025-40280, CVE-2025-40281, CVE-2025-40282, CVE-2025-40283, CVE-2025-40304, CVE-2025-40306, CVE-2025-40308, CVE-2025-40309, CVE-2025-40312, CVE-2025-40313, CVE-2025-40314, CVE-2025-40315, CVE-2025-40317, CVE-2025-40319, CVE-2025-40321, CVE-2025-40322, CVE-2025-40324, CVE-2025-40331, CVE-2025-40342, CVE-2025-40343, CVE-2025-40345, CVE-2025-40360, CVE-2025-40363, CVE-2025-61984, CVE-2025-61985, CVE-2025-68161, CVE-2025-68168, CVE-2025-68176, CVE-2025-68177, CVE-2025-68185, CVE-2025-68191, CVE-2025-68192, CVE-2025-68194, CVE-2025-68200, CVE-2025-68204, CVE-2025-68217, CVE-2025-68220, CVE-2025-68227, CVE-2025-68229, CVE-2025-68238, CVE-2025-68241, CVE-2025-68244, CVE-2025-68245, CVE-2025-68254, CVE-2025-68255, CVE-2025-68257, CVE-2025-68258, CVE-2025-68261, CVE-2025-68264, CVE-2025-68266, CVE-2025-68282, CVE-2025-68284, CVE-2025-68285, CVE-2025-68286, CVE-2025-68287, CVE-2025-68288, CVE-2025-68289, CVE-2025-68290, CVE-2025-68295, CVE-2025-68301, CVE-2025-68302, CVE-2025-68303, CVE-2025-68308, CVE-2025-68312, CVE-2025-68321, CVE-2025-68325, CVE-2025-68327, CVE-2025-68328, CVE-2025-68330, CVE-2025-68331, CVE-2025-68332, CVE-2025-68335, CVE-2025-68336, CVE-2025-68337, CVE-2025-68339, CVE-2025-68344, CVE-2025-68346, CVE-2025-68349, CVE-2025-68354, CVE-2025-68362, CVE-2025-68364, CVE-2025-68366, CVE-2025-68367, CVE-2025-68372, CVE-2025-68724, CVE-2025-68727, CVE-2025-68728, CVE-2025-68732, CVE-2025-68733, CVE-2025-68734, CVE-2025-68740, CVE-2025-68746, CVE-2025-68757, CVE-2025-68758, CVE-2025-68759, CVE-2025-68764, CVE-2025-68765, CVE-2025-68767, CVE-2025-68769, CVE-2025-68771, CVE-2025-68774, CVE-2025-68776, CVE-2025-68777, CVE-2025-68780, CVE-2025-68782, CVE-2025-68783, CVE-2025-68785, CVE-2025-68787, CVE-2025-68788, CVE-2025-68795, CVE-2025-68796, CVE-2025-68797, CVE-2025-68799, CVE-2025-68800, CVE-2025-68801, CVE-2025-68803, CVE-2025-68804, CVE-2025-68808, CVE-2025-68813, CVE-2025-68814, CVE-2025-68815, CVE-2025-68816, CVE-2025-68818, CVE-2025-68819, CVE-2025-68820, CVE-2025-68821, CVE-2025-71064, CVE-2025-71066, CVE-2025-71068, CVE-2025-71069, CVE-2025-71075, CVE-2025-71077, CVE-2025-71078, CVE-2025-71079, CVE-2025-71081, CVE-2025-71082, CVE-2025-71083, CVE-2025-71084, CVE-2025-71085, CVE-2025-71086, CVE-2025-71087, CVE-2025-71091, CVE-2025-71093, CVE-2025-71094, CVE-2025-71096, CVE-2025-71097, CVE-2025-71098, CVE-2025-71102, CVE-2025-71104, CVE-2025-71105, CVE-2025-71108, CVE-2025-71111, CVE-2025-71112, CVE-2025-71113, CVE-2025-71114, CVE-2025-71116, CVE-2025-71118, CVE-2025-71120, CVE-2025-71121, CVE-2025-71125, CVE-2025-71127, CVE-2025-71131, CVE-2025-71132, CVE-2025-71133, CVE-2025-71136, CVE-2025-71137, CVE-2025-71147, CVE-2025-71154, CVE-2025-71180, CVE-2025-71182, CVE-2026-0865, CVE-2026-1519, CVE-2026-1965, CVE-2026-22976, CVE-2026-22977, CVE-2026-22978, CVE-2026-22980, CVE-2026-22982, CVE-2026-22984, CVE-2026-22990, CVE-2026-22991, CVE-2026-22992, CVE-2026-23019, CVE-2026-23020, CVE-2026-23021, CVE-2026-23047, CVE-2026-23268, CVE-2026-23269, CVE-2026-25749, CVE-2026-26007, CVE-2026-26269, CVE-2026-27448, CVE-2026-27459, CVE-2026-2781, CVE-2026-28417, CVE-2026-28418, CVE-2026-28419, CVE-2026-28420, CVE-2026-28421, CVE-2026-28422, CVE-2026-29111, CVE-2026-30922, CVE-2026-3104, CVE-2026-3119, CVE-2026-3497, CVE-2026-3591, CVE-2026-3731, CVE-2026-3783, CVE-2026-3784, CVE-2026-3805
26.02.11 ExtremeAnalytics, and Application Analytics Traffic Sensor images:
CVE-2022-24765, CVE-2022-49267, CVE-2023-24626, CVE-2024-53114, CVE-2024-56538, CVE-2024-58011, CVE-2025-10148, CVE-2025-11187, CVE-2025-11468, CVE-2025-11563, CVE-2025-12084, CVE-2025-13034, CVE-2025-13837, CVE-2025-14017, CVE-2025-14524, CVE-2025-14819, CVE-2025-14831, CVE-2025-15079, CVE-2025-15224, CVE-2025-15281, CVE-2025-15282, CVE-2025-15366, CVE-2025-15367, CVE-2025-15467, CVE-2025-15468, CVE-2025-15469, CVE-2025-21780, CVE-2025-21861, CVE-2025-22058, CVE-2025-23143, CVE-2025-38236, CVE-2025-38248, CVE-2025-38584, CVE-2025-39869, CVE-2025-39873, CVE-2025-39876, CVE-2025-39880, CVE-2025-39883, CVE-2025-39885, CVE-2025-39907, CVE-2025-39911, CVE-2025-39913, CVE-2025-39923, CVE-2025-39934, CVE-2025-39937, CVE-2025-39943, CVE-2025-39945, CVE-2025-39949, CVE-2025-39951, CVE-2025-39953, CVE-2025-39955, CVE-2025-39967, CVE-2025-39968, CVE-2025-39969, CVE-2025-39970, CVE-2025-39971, CVE-2025-39972, CVE-2025-39973, CVE-2025-39980, CVE-2025-39985, CVE-2025-39986, CVE-2025-39987, CVE-2025-39988, CVE-2025-39994, CVE-2025-39995, CVE-2025-39996, CVE-2025-39998, CVE-2025-40001, CVE-2025-40006, CVE-2025-40011, CVE-2025-40020, CVE-2025-40021, CVE-2025-40026, CVE-2025-40027, CVE-2025-40029, CVE-2025-40030, CVE-2025-40035, CVE-2025-40042, CVE-2025-40043, CVE-2025-40044, CVE-2025-40048, CVE-2025-40049, CVE-2025-40053, CVE-2025-40055, CVE-2025-40060, CVE-2025-40068, CVE-2025-40070, CVE-2025-40078, CVE-2025-40081, CVE-2025-40085, CVE-2025-40087, CVE-2025-40088, CVE-2025-40092, CVE-2025-40094, CVE-2025-40105, CVE-2025-40106, CVE-2025-40109, CVE-2025-40111, CVE-2025-40112, CVE-2025-40115, CVE-2025-40116, CVE-2025-40118, CVE-2025-40120, CVE-2025-40121, CVE-2025-40124, CVE-2025-40125, CVE-2025-40126, CVE-2025-40127, CVE-2025-40134, CVE-2025-40140, CVE-2025-40153, CVE-2025-40154, CVE-2025-40167, CVE-2025-40171, CVE-2025-40173, CVE-2025-40178, CVE-2025-40179, CVE-2025-40183, CVE-2025-40187, CVE-2025-40188, CVE-2025-40194, CVE-2025-40200, CVE-2025-40204, CVE-2025-40205, CVE-2025-40215, CVE-2025-40219, CVE-2025-40220, CVE-2025-40223, CVE-2025-40231, CVE-2025-40233, CVE-2025-40240, CVE-2025-40243, CVE-2025-40244, CVE-2025-40245, CVE-2025-40346, CVE-2025-40349, CVE-2025-40351, CVE-2025-46802, CVE-2025-46804, CVE-2025-46805, CVE-2025-59375, CVE-2025-66199, CVE-2025-68160, CVE-2025-68249, CVE-2025-69418, CVE-2025-69419, CVE-2025-69420, CVE-2025-69421, CVE-2025-8058, CVE-2025-8277, CVE-2025-9086, CVE-2025-9820, CVE-2026-0672, CVE-2026-0861, CVE-2026-0865, CVE-2026-0915, CVE-2026-0964, CVE-2026-0965, CVE-2026-0966, CVE-2026-0967, CVE-2026-0968, CVE-2026-1484, CVE-2026-1485, CVE-2026-1489, CVE-2026-21936, CVE-2026-21937, CVE-2026-21941, CVE-2026-21948, CVE-2026-21964, CVE-2026-21968, CVE-2026-22795, CVE-2026-22796, CVE-2026-24515, CVE-2026-25210, CVE-2026-25646
26.02.11 ExtremeControl images:
CVE-2022-24765, CVE-2022-49267, CVE-2023-24626, CVE-2024-53114, CVE-2024-56538, CVE-2024-58011, CVE-2025-10148, CVE-2025-11187, CVE-2025-11468, CVE-2025-11563, CVE-2025-12084, CVE-2025-13034, CVE-2025-13837, CVE-2025-14017, CVE-2025-14524, CVE-2025-14819, CVE-2025-14831, CVE-2025-15079, CVE-2025-15224, CVE-2025-15281, CVE-2025-15282, CVE-2025-15366, CVE-2025-15367, CVE-2025-15467, CVE-2025-15468, CVE-2025-15469, CVE-2025-21780, CVE-2025-21861, CVE-2025-22058, CVE-2025-23143, CVE-2025-38236, CVE-2025-38248, CVE-2025-38584, CVE-2025-39869, CVE-2025-39873, CVE-2025-39876, CVE-2025-39880, CVE-2025-39883, CVE-2025-39885, CVE-2025-39907, CVE-2025-39911, CVE-2025-39913, CVE-2025-39923, CVE-2025-39934, CVE-2025-39937, CVE-2025-39943, CVE-2025-39945, CVE-2025-39949, CVE-2025-39951, CVE-2025-39953, CVE-2025-39955, CVE-2025-39967, CVE-2025-39968, CVE-2025-39969, CVE-2025-39970, CVE-2025-39971, CVE-2025-39972, CVE-2025-39973, CVE-2025-39980, CVE-2025-39985, CVE-2025-39986, CVE-2025-39987, CVE-2025-39988, CVE-2025-39994, CVE-2025-39995, CVE-2025-39996, CVE-2025-39998, CVE-2025-40001, CVE-2025-40006, CVE-2025-40011, CVE-2025-40020, CVE-2025-40021, CVE-2025-40026, CVE-2025-40027, CVE-2025-40029, CVE-2025-40030, CVE-2025-40035, CVE-2025-40042, CVE-2025-40043, CVE-2025-40044, CVE-2025-40048, CVE-2025-40049, CVE-2025-40053, CVE-2025-40055, CVE-2025-40060, CVE-2025-40068, CVE-2025-40070, CVE-2025-40078, CVE-2025-40081, CVE-2025-40085, CVE-2025-40087, CVE-2025-40088, CVE-2025-40092, CVE-2025-40094, CVE-2025-40105, CVE-2025-40106, CVE-2025-40109, CVE-2025-40111, CVE-2025-40112, CVE-2025-40115, CVE-2025-40116, CVE-2025-40118, CVE-2025-40120, CVE-2025-40121, CVE-2025-40124, CVE-2025-40125, CVE-2025-40126, CVE-2025-40127, CVE-2025-40134, CVE-2025-40140, CVE-2025-40153, CVE-2025-40154, CVE-2025-40167, CVE-2025-40171, CVE-2025-40173, CVE-2025-40178, CVE-2025-40179, CVE-2025-40183, CVE-2025-40187, CVE-2025-40188, CVE-2025-40194, CVE-2025-40200, CVE-2025-40204, CVE-2025-40205, CVE-2025-40215, CVE-2025-40219, CVE-2025-40220, CVE-2025-40223, CVE-2025-40231, CVE-2025-40233, CVE-2025-40240, CVE-2025-40243, CVE-2025-40244, CVE-2025-40245, CVE-2025-40346, CVE-2025-40349, CVE-2025-40351, CVE-2025-46802, CVE-2025-46804, CVE-2025-46805, CVE-2025-59375, CVE-2025-66199, CVE-2025-68160, CVE-2025-68249, CVE-2025-69418, CVE-2025-69419, CVE-2025-69420, CVE-2025-69421, CVE-2025-8058, CVE-2025-8277, CVE-2025-9086, CVE-2025-9820, CVE-2026-0672, CVE-2026-0861, CVE-2026-0865, CVE-2026-0915, CVE-2026-0964, CVE-2026-0965, CVE-2026-0966, CVE-2026-0967, CVE-2026-0968, CVE-2026-1484, CVE-2026-1485, CVE-2026-1489, CVE-2026-21936, CVE-2026-21937, CVE-2026-21941, CVE-2026-21948, CVE-2026-21964, CVE-2026-21968, CVE-2026-22795, CVE-2026-22796, CVE-2026-24515, CVE-2026-25210, CVE-2026-25646
26.02.11 ExtremeCloud IQ Site Engine images:
CVE-2025-12817, CVE-2025-12818, CVE-2022-24765, CVE-2022-49267, CVE-2023-24626, CVE-2024-53114, CVE-2024-56538, CVE-2024-58011, CVE-2025-10148, CVE-2025-11187, CVE-2025-11468, CVE-2025-11563, CVE-2025-12084, CVE-2025-13034, CVE-2025-13837, CVE-2025-14017, CVE-2025-14524, CVE-2025-14819, CVE-2025-14831, CVE-2025-15079, CVE-2025-15224, CVE-2025-15281, CVE-2025-15282, CVE-2025-15366, CVE-2025-15367, CVE-2025-15467, CVE-2025-15468, CVE-2025-15469, CVE-2025-21780, CVE-2025-21861, CVE-2025-22058, CVE-2025-23143, CVE-2025-38236, CVE-2025-38248, CVE-2025-38584, CVE-2025-39869, CVE-2025-39873, CVE-2025-39876, CVE-2025-39880, CVE-2025-39883, CVE-2025-39885, CVE-2025-39907, CVE-2025-39911, CVE-2025-39913, CVE-2025-39923, CVE-2025-39934, CVE-2025-39937, CVE-2025-39943, CVE-2025-39945, CVE-2025-39949, CVE-2025-39951, CVE-2025-39953, CVE-2025-39955, CVE-2025-39967, CVE-2025-39968, CVE-2025-39969, CVE-2025-39970, CVE-2025-39971, CVE-2025-39972, CVE-2025-39973, CVE-2025-39980, CVE-2025-39985, CVE-2025-39986, CVE-2025-39987, CVE-2025-39988, CVE-2025-39994, CVE-2025-39995, CVE-2025-39996, CVE-2025-39998, CVE-2025-40001, CVE-2025-40006, CVE-2025-40011, CVE-2025-40020, CVE-2025-40021, CVE-2025-40026, CVE-2025-40027, CVE-2025-40029, CVE-2025-40030, CVE-2025-40035, CVE-2025-40042, CVE-2025-40043, CVE-2025-40044, CVE-2025-40048, CVE-2025-40049, CVE-2025-40053, CVE-2025-40055, CVE-2025-40060, CVE-2025-40068, CVE-2025-40070, CVE-2025-40078, CVE-2025-40081, CVE-2025-40085, CVE-2025-40087, CVE-2025-40088, CVE-2025-40092, CVE-2025-40094, CVE-2025-40105, CVE-2025-40106, CVE-2025-40109, CVE-2025-40111, CVE-2025-40112, CVE-2025-40115, CVE-2025-40116, CVE-2025-40118, CVE-2025-40120, CVE-2025-40121, CVE-2025-40124, CVE-2025-40125, CVE-2025-40126, CVE-2025-40127, CVE-2025-40134, CVE-2025-40140, CVE-2025-40153, CVE-2025-40154, CVE-2025-40167, CVE-2025-40171, CVE-2025-40173, CVE-2025-40178, CVE-2025-40179, CVE-2025-40183, CVE-2025-40187, CVE-2025-40188, CVE-2025-40194, CVE-2025-40200, CVE-2025-40204, CVE-2025-40205, CVE-2025-40215, CVE-2025-40219, CVE-2025-40220, CVE-2025-40223, CVE-2025-40231, CVE-2025-40233, CVE-2025-40240, CVE-2025-40243, CVE-2025-40244, CVE-2025-40245, CVE-2025-40346, CVE-2025-40349, CVE-2025-40351, CVE-2025-46802, CVE-2025-46804, CVE-2025-46805, CVE-2025-59375, CVE-2025-66199, CVE-2025-68160, CVE-2025-68249, CVE-2025-69418, CVE-2025-69419, CVE-2025-69420, CVE-2025-69421, CVE-2025-8058, CVE-2025-8277, CVE-2025-9086, CVE-2025-9820, CVE-2026-0672, CVE-2026-0861, CVE-2026-0865, CVE-2026-0915, CVE-2026-0964, CVE-2026-0965, CVE-2026-0966, CVE-2026-0967, CVE-2026-0968, CVE-2026-1484, CVE-2026-1485, CVE-2026-1489, CVE-2026-21936, CVE-2026-21937, CVE-2026-21941, CVE-2026-21948, CVE-2026-21964, CVE-2026-21968, CVE-2026-22795, CVE-2026-22796, CVE-2026-24515, CVE-2026-25210, CVE-2026-25646
26.02.10 ExtremeAnalytics, and Application Analytics Traffic Sensor images:
CVE-2016-9843, CVE-2021-46848, CVE-2025-13151, CVE-2025-13601, CVE-2025-13836, CVE-2025-14087, CVE-2025-3360, CVE-2025-6052, CVE-2025-66293, CVE-2025-68276, CVE-2025-68468, CVE-2025-68471, CVE-2025-68615, CVE-2025-68973, CVE-2025-69277, CVE-2025-7039, CVE-2025-8732, CVE-2026-0988, CVE-2026-0989, CVE-2026-0990, CVE-2026-0992, CVE-2026-21441, CVE-2026-21925, CVE-2026-21932, CVE-2026-21933, CVE-2026-21945, CVE-2026-22695, CVE-2026-22801, CVE-2026-23490.
26.02.10 ExtremeControl images:
CVE-2016-9843, CVE-2021-46848, CVE-2025-13151, CVE-2025-13601, CVE-2025-13836, CVE-2025-14087, CVE-2025-3360, CVE-2025-6052, CVE-2025-66293, CVE-2025-68276, CVE-2025-68468, CVE-2025-68471, CVE-2025-68615, CVE-2025-68973, CVE-2025-69277, CVE-2025-7039, CVE-2025-8732, CVE-2026-0988, CVE-2026-0989, CVE-2026-0990, CVE-2026-0992, CVE-2026-21441, CVE-2026-21925, CVE-2026-21932, CVE-2026-21933, CVE-2026-21945, CVE-2026-22695, CVE-2026-22801, CVE-2026-23490, CVE-2025-14180, CVE-2025-14177, CVE-2025-14178.
26.02.10 ExtremeCloud IQ Site Engine images:
CVE-2016-9843, CVE-2021-46848, CVE-2025-13151, CVE-2025-13601, CVE-2025-13836, CVE-2025-14087, CVE-2025-3360, CVE-2025-6052, CVE-2025-66293, CVE-2025-68276, CVE-2025-68468, CVE-2025-68471, CVE-2025-68615, CVE-2025-68973, CVE-2025-69277, CVE-2025-7039, CVE-2025-8732, CVE-2026-0988, CVE-2026-0989, CVE-2026-0990, CVE-2026-0992, CVE-2026-21441, CVE-2026-21925, CVE-2026-21932, CVE-2026-21933, CVE-2026-21945, CVE-2026-22695, CVE-2026-22801, CVE-2026-23490.
Installation, Upgrade, and Configuration Changes
Installation Information
For license requirements for ExtremeCloud IQ Site Engine and devices, see Licensing.
For complete installation instructions, see ExtremeCloud IQ Site Engine Suite Installation.
Upgrading Without an Internet Connection
!!! ATTENTION !!!
We can attempt to upgrade the OS without using the internet if there were no extra Ubuntu packages installed. If there were extraneous packages installed, the upgrade will fail with this method.
Do you want to attempt a local in-place upgrade of the OS and reboot when complete? (Y/n)Custom FlexViews
When reinstalling ExtremeCloud IQ Site Engine Console, the installation program saves copies of any FlexViews you created or modified in the <install directory>\.installer\backup\current\appdata\System\FlexViews folder.
If you are deploying FlexViews via the ExtremeCloud IQ Site Engine server, save them in the appdata\VendorProfiles\Stage\MyVendorProfile\FlexViews\My FlexViews folder.
Custom MIBs and Images
If you are deploying MIBs via the ExtremeCloud IQ Site Engine server, they are saved in the appdata\VendorProfiles\Stage\MyVendorProfile\MIBs\ folder.
If you are deploying device images (pictures) via the ExtremeCloud IQ Site Engine server, they are saved in the appdata\VendorProfiles\Stage\MyVendorProfile\Images\ folder.
Important Upgrade Information
A special MySQL to PostgreSQL Data Migration (For Upgrades from ExtremeCloud IQ Site Engine 24.2 to 24.7 or up to 25.8) is required to upgrade ExtremeCloud IQ Site Engine from versions older than 24.07. The minimum version to upgrade Analytics Engines and Access Control Engines is 24.02.13.
| NOTE: |
ExtremeCloud IQ Site Engine Version 26.02.13 contains an OS upgrade. If upgrading from version 24.02.15 then internet connectivity is required to download custom packages. The installer prompts "Do you want to use the Internet to perform the OS upgrade?". The offline upgrade path is supported when no custom packages are installed (answer N). The online upgrade is required when custom packages are manually installed (answer Y). An online upgrade is recommended when an online upgrade was used previously, however there is a risk of session timeout due to 15 minutes of screen inactivity. To upgrade Access Control Engines and Application Analytics Engines you can use the directive --keepalive to decrease the chance of a session expiry timeout from 15 minutes of no screen activity. |
| From Version (currently running) | To Version (next step in upgrade path) |
|---|---|
| ExtremeCloud IQ Site Engine 24.07.x, 24.10.x. 25.02.x, 25.05.x. 25.08.x, 25.11.x, 26.02.x | ExtremeCloud IQ Site Engine 26.02 |
| Application Analytics Engine, Access Control Engine 24.02.15, 24.07.x, 24.10.x, 25.02.x, 25.05.x, 25.08.x, 25.11.x, 26.02.x | Application Analytics Engine, Access Control Engine 26.02 |
| ExtremeCloud IQ Site Engine 24.02.x | Fresh installation of ExtremeCloud IQ Site Engine 25.08 and follow the MySQL to PostgreSQL Data Migration (For Upgrades from ExtremeCloud IQ Site Engine 24.2 to 24.7 or up to 25.8) |
| ExtremeCloud IQ Site Engine 23.04.12, 23.07.x, 23.11.x, 24.02.x | ExtremeCloud IQ Site Engine 24.02.15 |
| Application Analytics Engine, Access Control Engine 23.04.12, 23.07.x, 23.11.x, 24.02.x | Application Analytics Engine, Access Control Engine 24.02.15 |
| ExtremeCloud IQ Site Engine 21.x, 22.x, 23.2.x 23.04.10, 23.04.11 | ExtremeCloud IQ Site Engine 23.04.12 |
| Application Analytics Engine, Access Control Engine 21.x, 22.x, 23.2.x, 23.04.10, 23.04.11 | Application Analytics Engine, Access Control Engine 23.04.12 |
| Extreme Management Center version 8.5.7 | ExtremeCloud IQ Site Engine 24.02.15 |
| Extreme Management Center version 8.2.x to 8.5.6 | Extreme Management Center 8.5.7 |
| Extreme Management Center version 8.0.x to 8.1.x | Extreme Management Center 8.3.3.11 |
| NetSight version 7.1.4.1 | Extreme Management Center 8.3.3.11 |
| NetSight version 7.x | NetSight 7.1.4.1 |
| NetSight version 6.3.0.186 | NetSight 7.1.4.1 |
| NetSight version 6.x | NetSight 6.3.0.186 |
| IMPORTANT: | A backup (Administration > Backup/Restore) of the database must be performed prior to the upgrade and saved to a safe location. |
|---|
If you use LDAPS with a Fully Qualified Domain Name (FQDN) in the URL to authorize a user to the OneView, then ExtremeCloud IQ Site Engine presents the Server Certificate (located in Administration > Certificates > Server Certificate Information) to the LDAPS server. If the LDAPS server presents a certificate that does not match the LDAPS URL, then the certificate is rejected with the error “Certificate Unknown”.
The best practice is to use a trusted certificate if the LDAPS URL is defined with FQDN, otherwise the LDAPS server might not accept the LDAPs connection. The alternative option is to use an IP address in the LDAPS URL instead of FQDN.
Important Upgrade Considerations
- If your network is using ExtremeAnalytics or ExtremeControl engines, or another add-on feature, you must first perform the ExtremeCloud IQ Site Engine upgrade to version 26.02.13 and then upgrade the feature.
- To upgrade Traffic Sensor from version 21.x, a fresh installation is recommended. If the fresh installation cannot be used, then please check Knowledge Base for a special procedure.
- If the online upgrade fails due to an Internet connectivity issue, fix the connectivity issue and rerun the upgrade.
| IMPORTANT: | When performing an upgrade, be sure to back up the database prior to performing the upgrade, and save it to a safe location. Use the Administration > Backup/Restore tab to perform the backup. |
- When upgrading the ExtremeCloud IQ Site Engine server, ExtremeAnalyticsengine, or ExtremeControlengine to version 26.02.13, ensure the DNS server IP address is correctly configured.
-
When upgrading to ExtremeCloud IQ Site Engine version 26.02.13, if you adjusted the ExtremeCloud IQ Site Engine memory settings and want them to be saved on upgrade, a flag (
-DcustomMemory) needs to be added to the/usr/local/Extreme_Networks/NetSight/services/nsserver.cfgfile.
For example:-Xms12g -Xmx24g -XX:HeapDumpPath=../../nsdump.hprof -XX:+HeapDumpOnOutOfMemoryError -XX:MetaspaceSize=128m -DcustomMemory
License Renewal
Upgrading to ExtremeCloud IQ Site Engine version 26.02.13 requires you to transition from perpetual to subscription-based license model. Existing NMS licenses do not provide access to ExtremeCloud IQ Site Engine. If your perpetual licenses were not transitioned to subscription-based licenses, contact your Extreme Networks Representative for assistance.
Free Space Consideration
When upgrading to ExtremeCloud IQ Site Engine version 26.02.13, a minimum of 15 GB of free disk space is required on the ExtremeCloud IQ Site Engine server
To increase the amount of free disk space on the ExtremeCloud IQ Site Engine server, perform the following:
- Decrease the number of ExtremeCloud IQ Site Engine backups (by default, saved in the
/usr/local/Extreme_Networks/NetSight/backupdirectory). - Decrease the Data Persistence settings (Administration > Options > Access Control > Data Persistence).
- Remove unnecessary archives (Network > Archives).
-
Delete the files in the
<installation directory>/NetSight/.installerdirectory.
Site Discover Consideration
Discovering devices via the Site tab using a Range, Subnet, or Seed discover might not successfully add all expected devices. To correct the issue, increase the Length of SNMP Timeout value on the Administration > Options > Site tab in the Discover First SNMP Request section.
ExtremeAnalytics Upgrade Information
Enabling or disabling the disk flow export feature might cause enforce operations to time out. Enforcing again resolves the issue.
When you delete an ExtremeXOS/Switch Engine device that is configured as a flow source via the Flow Sources table of the
Analytics > Configuration > Engines > Configuration tab from the Devices list on the Network > Devices tab, an error message is generated in the server.log. The message does not warn you that the device is in use as a flow source. Adding the device back in the Devices list on the Network > Devices tab or removing the device from the Flow Source table fixes the issue.
The Flow Sources table on the Analytics > Configuration > engine > Configuration tab may take a few minutes to load.
ExtremeControl Version 8.0 and later
Beginning in version 8.0, ExtremeControl may fail to join Active Directory when accessing as a Standard Domain User with Descendant Computer Objects ("Reset password" permissions only) group member.
To allow this functionality, add the following permissions:
- Reset Password
- Validated write to DNS host name
- Validated write to service principal
- Read and write account restrictions
- Read and write DNS host name attributes
- Write servicePrincipalName
Other Upgrade Information
Immediately after you install version 26.02.13 on the ExtremeControlengine, the date and time does not properly synchronize and the following error message displays:
WARNING: Unable to synchronize to a NTP server. The time might not be correctly set on this device.
Ignore the error message and the date and time automatically synchronize after a short delay.
Additionally, the following message might display during the ExtremeControl upgrade to version 26.02.13:
No domain specified
To stop domain-specific winbindd process, run /etc/init.d/winbindd stop {example-domain.com}
Upgrading ExtremeControl Engine to Version 26.02.13
General Upgrade Information
The EAP-TLS Certificates with SHA1 are considered weak and are not accepted anymore. The radius server fails to start with the SHA1 certificate. You can use a more secure certificate, such as SHA256.
You are not required to upgrade your ExtremeControl engine version to 26.02.13 when upgrading to ExtremeCloud IQ Site Engine version 26.02.13. However, both ExtremeCloud IQ Site Engine and ExtremeControl engine must be at version 26.02.13 in order to take advantage of the new ExtremeControl version 26.02.13 features. ExtremeCloud IQ Site Engine version 26.02.13 supports managing ExtremeControl engine versions 23.x and up to 26.02.13.
In addition, if your ExtremeControl solution utilizes a Nessus assessment server, you should also upgrade your assessment agent adapter to version 26.02.13 if you upgrade to ExtremeControl version 26.02.13.
You can download the latest ExtremeControl engine version at the Extreme Portal.
LDAPS servers with FQDN
If the LDAPS server URL uses a Fully Qualified Domain Name (FQDN), then the LDAPS client of Access Control Engine presents the internal Communication Certificate to the LDAPS server. If the LDAPS server URL uses a FQDN then the LDAPS client of ExtremeCloud IQ Site Engine presents the Server Certificate (located in Administration > Certificates > Server Certificate Information) to the LDAPS server. If the LDAPS server presents a certificate that does not match the LDAPS URL, then the certificate is rejected with the error “Certificate Unknown”
The best practice is to use trusted certificates if the LDAPS URL is defined with FQDN, otherwise the LDAPS server might not accept the LDAPS connection. If the LDAPS server URL uses an IP address then the LDAPS client (of both Access Control Engine and ExtremeCloud IQ Site Engine) does not present the Certificate to the LDAPS server.
Upgrading to Policy Manager 26.02.13
- Policy Manager 26.02.13 only supports ExtremeWireless Controller version 8.01.03 and higher. If you upgrade to ExtremeCloud IQ Site Engine 26.02.13 prior to upgrading your controllers, then Policy Manager does not allow you to open a domain where the controllers already exist or add them to a domain. A dialog is displayed indicating your controllers do not meet minimum version requirements and that they must be upgraded before they can be in a domain.
- Following an upgrade to Wireless Controller version 8.31 and higher, a Policy Manager enforce fails if it includes changes to the default access control or any rules that are set to contain. To allow Policy Manager to modify the default access control or set rules to contain, you must disable the "Allow" action in policy rules contains to the VLAN assigned by the role checkbox accessed from the Wireless Controller's web interface on the Roles > Policy Rules tab. This will allow the enforce operation to succeed.
Fabric Configuration Information
Certificate
Fabric Manager might be unavailable via ExtremeCloud IQ Site Engine after upgrading if the certificate is missing in ExtremeCloud IQ Site Engine Trust store.
To ensure Fabric Manager is available, enter the Fabric Manager certificate in the ExtremeCloud IQ Site Engine Trust store using Generate Certificate option. See Add Fabric Manager Certificate for the certificate procedure.
Authentication Key
When you provision authentication keys for Fabric Attach, the key cannot be read back for security reasons. When the key is read from the device, it always shows "****". For this reason, it might seem that there is a configuration mismatch when one does not exist.
Service Configuration Change
If you change a configured service via the Configure Device window that references one of the following, and then enforce those changes to the device, the configuration on the device might change unexpectedly:
- MLT
- SMLT
- Port-specific settings to a port belonging to an MLT or SMLT
To prevent this merge, change rows in the Enforce Preview window where MLT or SMLT are in use from Current to Desired.
To correct the issue after enforcement, modify the service on the device via the CLI.
CLIP Addresses
Using the CLIP Addresses table in the Configure Device window, you can enter addresses in both IPv4 and IPv6 formats. However, ExtremeCloud IQ Site Engine version 26.02.13 only supports applying a single address (either IPv4 or IPv6) to a Loopback Interface.
Upgrading VSP-8600
When upgrading from Extreme Management Center version 8.2 to version 8.3. manually reload previously discovered VSP-8600 devices to gain access to Fabric Connect features.
Removing Fabric Connect Configuration
Removing a device's Fabric Connect configuration by setting the Topology Definition to <None> may fail if the device has Logical Interfaces assigned to ISIS.
Password Configuration
Fabric Manager fails to onboard in ExtremeCloud IQ Site Engine if the root password includes an ampersand (&) character. Additionally, if the Administration > Inventory Manager > SCP tab contains a password that includes an ampersand (&) in ExtremeCloud IQ Site Engine, the Fabric Manager firmware does not download successfully.
Ensure you use a password without an ampersand (&) character.
VRF Configuration
Fabric Engine SNMP performance is adversely affected as the number of VRF configurations increases. This issue can be resolved by upgrading toFabric Engine release 8.1.1 or later or VSP-8600 series version 6.3.3 or later.
Device Configuration Information
VDX Device Configuration
To properly discover interfaces and links for VDX devices in ExtremeCloud IQ Site Engine, enable three-tuple-if on the device.
| NOTE: | To enable three-tuple-if on the device in ExtremeCloud IQ Site Engine:
|
Additionally, for ExtremeCloud IQ Site Engine to display VCS fabric , the NOS version must be 7.2.0a or later.
Rediscover VDX devices after upgrading to ExtremeCloud IQ Site Engine.
Fabric Engine Device Configuration
Topology links from Fabric Engine devices to other Fabric Engine or ERS devices might not display in a topology map (or might display inconsistently). To ensure topology map links display correctly, verify that the Fabric Engine device is configured to publish its management IP address in the autotopology (SONMP) data.
Ensure that the output of show sys setting command shows:
autotopology : on
ForceTopologyIpFlag : true
clipId-topology-ip : 0
If the output values displayed are different, configure the Fabric Engine device to publish management IP address in SONMP data by executing the following CLI commands:
(config)# autotopology
(config)# sys force-topology-ip-flag enable
(config)# default sys clipId-topology-ip
The Status of LAG links in maps will start working after the next polling following an upgrade to ExtremeCloud IQ Site Engine. You can initiate the polling of a device by performing a refresh/rediscovery of the device.
ERS Device Configuration
ERS devices might automatically change VLAN configurations you define in ExtremeCloud IQ Site Engine. To disable this, change the vlan configcontrol setting for ERS devices you add to ExtremeCloud IQ Site Engine by entering the following in the device command line:
CLI commands
enable
config term
vlan configcontrol flexible
Additionally, configure all VLANs on the port for an ERS device with the same tag status (tagged or untagged). If enforcing to an ERS device on which a port has at least one VLAN as tagged, ExtremeCloud IQ Site Engine adds all untagged VLANs to the tagged VLAN list and clears the untagged VLAN list.
Creating an archive for ERS devices using the Network > Archives tab does not complete successfully if Menu mode (cmd-interface menu) is used instead of CLI mode (cmd-interface cli). See
SLX Device Configuration
When creating a ZTP+ Configuration for an SLX 9240 on which firmware version 18s.01.01 or 18s.01.02 is installed, the ZTP+ process fails if the Administration Profile value uses SSH or Telnet CLI credentials. ExtremeCloud IQ Site Engine indicates that the SSH or CLI profile is not supported by the device.
To create a ZTP+ configuration for an SLX 9240:
- Create a new Device Profile with the CLI Credential set to < No Access >.
- Create the ZTP+ Configuration and select the new Device Profile you created in Step 1 as the Administration Profile.
- After the ZTP+ process successfully completes and the device is added to ExtremeCloud IQ Site Engine, select a Device Profile that uses the correct CLI credentials for the SLX device in the Administration Profile.
| NOTE: | The SLX ZTP+ Connector does NOT support configuring CLI credentials on the device. |
ExtremeXOS Device Configuration
ExtremeXOS/Switch Engine devices on which firmware version 30.3.1.6 is installed do not download and install new firmware versions successfully via the ZTP+ process. To correct the issue, access the Network > Firmware tab in ExtremeCloud IQ Site Engine, select the ExtremeXOS device you are updating via ZTP+, and change the Version field in the Details right-panel from builds/xos_30.3/30.3.1.6 to 30.3.1.6.
Firmware Upgrade Configuration Information
ExtremeCloud IQ Site Engine supports firmware downloads and uploads to devices using TFTP, FTP, SCP, and SFTP. However, before firmware images can be downloaded or uploaded from the server, ExtremeCloud IQ Site Engine needs the root path or directory for each of the protocols. The following default root paths for each protocol are configurable from the Administration > Options > Inventory Manager tab:
Protocol Root Path:
- TFTP: /tftpboot/firmware/images/
- FTP: /tftpboot/firmware/images/
- SCP: /root/firmware/images/
- SFTP: /root/firmware/images/
To upload firmware images that are 2 GB or less to the server, use the ExtremeCloud IQ Site EngineNetwork > Firmware tab. For files larger than 2 GB, use a third-party client (such as SCP, WinSCP, or FTP).
For example, to use SCP to upload a firmware image to the SCP root path on the server, enter the following:
scp <LOCAL_FIRMWARE_PATH> root@<ExtremeCloud IQ Site Engine_SERVER_IP>:/root/firmware/images- Where:
- <ExtremeCloud IQ Site Engine_SERVER_IP>= IP Address to ExtremeCloud IQ Site Engine Server
- <LOCAL_FIRMWARE_PATH>= fully qualified path to a firmware image on the client machine
Wireless Manager Upgrade Information
A High Availability pair cannot be added as a flow source if the WLAN(s) selected are not in common with both wireless controllers.
Server and Client System Requirements
| IMPORTANT: | Wireless event collection is disabled by default in version 26.02.13 due to the increase in disk space usage required. To enable event collection, select Enable Event CollectionEvent Analyze. Then select Administration > Options > Event Analyze. Internet Explorer is not supported in ExtremeCloud IQ Site Engine version 26.02.13. |
Operating System Requirements
ExtremeCloud IQ Site Engine Server Requirements
| Manufacturer | Operating System |
|---|---|
| Linux | Red Hat Enterprise Linux 9.7 |
| VMware® (ExtremeCloud IQ Site Engine Virtual Engine) |
VMware ESXi™ 6.0 server |
| Microsoft® Hyper-V (ExtremeCloud IQ Site Engine Virtual Engine) | Windows® Server 2019 Windows® Server 2022 |
| Nutanix (ExtremeCloud IQ Site Engine Virtual Engine) | AHV: 20230302.101026 AOS: 6.8.1 Prism Central: 2024.2 |
| Extreme Networks | Universal Compute Platform 2130C version 5.09.01 |
These are the operating system requirements for the ExtremeCloud IQ Site Engine server.
ExtremeCloud IQ Site Engine Client Requirements
These are the operating system requirements for remote ExtremeCloud IQ Site Engine client machines.
| Manufacturer | Operating System |
|---|---|
| Windows (qualified on the English version of the operating systems) | Windows® 10 and 11 |
| Linux | Red Hat Enterprise Linux 9.7 |
| Mac OS X® | Monterey, Sonoma |
ExtremeCloud IQ Site Engine Server and Client Hardware Requirements
These are the hardware requirements for the ExtremeCloud IQ Site Engine server and ExtremeCloud IQ Site Engine client machines.
| NOTES: | ExtremeControl and ExtremeAnalytics are not supported on Small ExtremeCloud IQ Site Engine servers. |
ExtremeCloud IQ Site Engine Server Requirements
| Small | Medium | Enterprise | Large Enterprise | |
|---|---|---|---|---|
| Total CPUs | 1 | 2 | 2 | 2 |
| Total CPU Cores | 8 | 16 | 24 | 24 |
| Memory | 16 GB | 32 GB | 64 GB | 64 GB |
| Disk Size | 240 GB | 480 GB | 960 GB | 1.92 TB |
| IOPS | 200 | 200 | 10,000 | 10,000 |
|
Recommended scale based on server configuration: |
||||
| Maximum APs | 250 | 2,500 | 25,000 | 25,000 |
| Maximum Wireless MUs | 2,500 | 25,000 | 100,000 | 100,000 |
| Maximum XIQ Controllers | 2 | 4 | 100 | 100 |
| Maximum Managed Devices | 100 | 1,000 | 10,000 air gap 8,000 connected |
10,000 air gap 8,000 connected |
| Maximum Concurrent Management Sessions | 5 | 15 | 50 | 50 |
| ExtremeControl End-Systems | N/A | 50,000 | 200,000 | 200,000 |
| Statistics Retention (Days) | 90 | 180 | 180 | 360 |
| ExtremeAnalytics | No | Yes | Yes | Yes |
| MU Events | No | Yes | Yes | Yes |
| IMPORTANT: | For optimal performance the CPU and Memory needs to reserved in the ESX Client and the virtual machine needs to be deployed using Thick Disk provisioning. |
ExtremeCloud IQ Site Engine Client Requirements
| Requirements | |
|---|---|
| CPU Speed | Dual Core Processor |
| Memory | 8 GB |
| Disk Size | 300 MB (User's home directory requires 50 MB for file storage) |
| Java Runtime Environment (JRE) (Oracle Java only) | Version 8 (for FlexView Editor / MIB Tools) |
| Browser1 (Enable JavaScript and Cookies) | Microsoft Edge Mozilla Firefox Google Chrome |
1Browsers set to a zoom ratio of less than 100% might not display ExtremeCloud IQ Site Engine properly (for example, missing borders around windows). Setting your browser to a zoom ratio of 100% corrects this issue.
Virtual Engine Requirements
The ExtremeCloud IQ Site Engine, ExtremeControl, and ExtremeAnalytics virtual engines must be deployed on a VMware, Hyper-V server, Nutanix, or Extreme Networks Universal Compute Platform.
- ExtremeCloud IQ Site Engine and virtual engines are packaged in the .OVA file format for VMware deployment.
- ExtremeCloud IQ Site Engine and virtual engines are packaged in the .ZIP file format for Hyper-V deployment.
- ExtremeCloud IQ Site Engine and virtual engines are packaged in the .OVA file format for deployment to the Nutanix through Prism Central.
- ExtremeCloud IQ Site Engine and virtual engines are packaged in the .TAR file format for deployment to the Universal Compute Platform.
| IMPORTANT: | For ESX and Hyper-V servers configured with AMD processors, the ExtremeExtremeAnalytics virtual engine requires AMD processors with at least Bulldozer based Opterons. |
ExtremeCloud IQ Site Engine Virtual Engine Requirements
| Specifications | Small | Medium | Enterprise | UCP 2130C |
|---|---|---|---|---|
| Total CPU Cores | 8 | 16 | 24 | N/A |
| Memory | 16 GB | 32 GB | 64 GB | N/A |
| Disk Size | 240 GB | 480 GB | 960 GB | N/A |
| IOPS | 200 | 200 | 10,000 | N/A |
|
Recommended scale based on server configuration: |
||||
| Maximum APs | 250 | 2,500 | 25,000 | 25.000 |
| Maximum Wireless MUs | 2,500 | 25,000 | 100,000 | 100,000 |
| Maximum XIQ Controllers | 2 | 4 | 100 | 100 |
| Maximum Managed Devices | 100 | 1,000 | 10,000 air gap 8,000 connected |
10,000 air gap 8,000 connected |
| Maximum Concurrent Management Sessions | 5 | 15 | 50 | 50 |
| ExtremeControl End-Systems | N/A | 50,000 | 200,000 | 200,000 |
| Statistics Retention (Days) | 90 | 180 | 180 | 180 |
| ExtremeAnalytics | No | Yes | Yes | Yes |
| MU Events | No | Yes | Yes | Yes |
| IMPORTANT: | For optimal performance the CPU and Memory needs to reserved in the ESX Client and the virtual machine needs to be deployed using Thick Disk provisioning. |
ExtremeControl Virtual Engine Requirements
| Specifications | Small | Medium | Enterprise | Large Enterprise | UCP 2130C |
|---|---|---|---|---|---|
| Total CPU Cores | 8 | 16 | 16 | 20 | N/A |
| Memory | 12 GB | 16 GB | 32 GB | 48 GB | N/A |
| Disk Size | 40 GB | 120 GB | 120 GB | 120 GB | N/A |
| IOPS | 200 | 200 | 200 | 200 | N/A |
|
Recommended scale based on server configuration: |
|||||
| ExtremeControl End-Systems | 3,000 | 6,000 | 9,000/12,0001 | 12,000/24,0002 | 12,000/24,0002 |
| Authentication | Yes | Yes | Yes | Yes | Yes |
| Captive Portal | No | Yes | Yes/No1 | Yes/No2 | Yes/No2 |
| Assessment | No | Yes | No | No | No |
1 The Enterprise ExtremeControlengine configuration supports two different scale options:
|
|||||
2 The Large Enterprise ExtremeControlengine configuration supports two different scale options:
|
|||||
| IMPORTANT: | For optimal performance the CPU and Memory needs to reserved in the ESX Client and the virtual machine needs to be deployed using Thick Disk provisioning. |
ExtremeAnalytics Virtual Engine Requirements
| Specifications | Small | Medium | Enterprise | UCP 2130C |
|---|---|---|---|---|
| Total CPU Cores | 8 | 16 | 16 | N/A |
| Memory | 12 GB | 32 GB | 64 GB | N/A |
| Disk Size | 40 GB | 480 GB | 960 GB | N/A |
| IOPS | 200 | 10,000 | 10,000 | N/A |
|
Recommended scale based on server configuration: |
||||
| Flows Per Minute | 250,000 | 500,000 | 750,000 | 750,000 |
| End-Systems | 10,000 | 20,000 | 30,000 | 30,000 |
| Raw Flow Retention (Days) | 3.5 | 3.5 | 7 | 7 |
| IMPORTANT: |
The ESXi free license supports a maximum of 8 CPU cores, and the medium and enterprise ExtremeAnalytics virtual engine installations require 16 CPU cores. Sixteen CPU cores are only available by purchasing a permanent license. To use the ExtremeAnalytics virtual engine with an ESXi free license, adjust the number of CPU cores to 8. To reduce the possibility of impaired functionality, ensure at least 4 GB of swap space is available for flow storage on the ExtremeAnalytics virtual engine. To verify the amount of
available RAM on your Linux system, use the |
Fabric Manager Requirements
| Specifications | Requirements |
|---|---|
| Total CPU Cores | 4 |
| Memory | 9 GB |
| Memory allocated to Java: -Xms -Xmx |
4 GB 6 GB |
| Disk Size | 60 GB |
ExtremeControl Captive Portal Supported End-System Browsers
The following table outlines the supported desktop and mobile end-system browsers connecting to the network through the Mobile Captive Portal of Extreme NetworksExtremeControl.
| Medium | Browser |
|---|---|
| Desktop | Microsoft Edge Microsoft Internet Explorer Mozilla Firefox Google Chrome |
| Mobile | Internet Explorer Mobile Microsoft Edge Microsoft Windows 10 Touch Screen Native (Surface Tablet) iOS Native Android Chrome Android Native Dolphin Opera |
| NOTES: | A native browser indicates the default, system-installed browser. Although this might be Chrome (Android), this also includes the default, system-controlled browser used for a device’s Captive Network Detection for a device. Typically, this is a non-configurable option for Wi-Fi Captive Network Detection, but default Android, Microsoft and iOS devices are tested for compatibility with the Mobile Captive Portal. A mobile device can access the standard (non-mobile) version of the Captive Portal using any desktop-supported browsers available on a mobile device. |
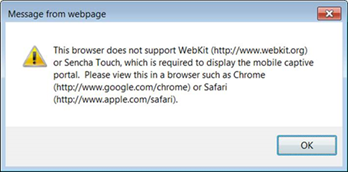
For other browsers, the Mobile Captive Portal requires the browser on the mobile device to be compatible with Webkit or Sencha Touch.
To confirm compatibility with Webkit or Sencha Touch, open http://<ExtremeControlEngine IP>/mobile_screen_preview using your mobile web browser.
- If the browser is compatible, the page displays properly.
- If the browser is not compatible with the Mobile Captive Portal, the following error displays:
ExtremeControl Engine Version Requirements
For complete information on ExtremeControl engine version requirements, see Important Upgrade Information.
ExtremeControl VPN Integration Requirements
VPN concentrators are supported for use in ExtremeControl VPN deployment scenarios.
- Supported Functionality: Authentication and Authorization (policy enforcement)
Cisco ASA
Enterasys XSR - Supported Functionality: Authentication
Juniper SA (requires an S-Series Stand Alone (SSA) system in order to provide access control)
| NOTE: | For all ExtremeControl VPN Deployment scenarios, an S-Series Stand Alone (SSA) system is required to change authorization levels beyond the initial authorization, such as when using assessment. |
ExtremeControl SMS Gateway Requirements
The following SMS Gateways have been tested for interoperability with ExtremeControl:
- Clickatell
- Mobile Pronto
ExtremeControl SMS Text Messaging Requirements
The following mobile service providers are supported by default for SMS text messaging in an ExtremeControl deployment. Additional service providers can be added:
| AT&T | Sprint PCS |
| Alltel | SunCom |
| Bell Mobility (Canada) | T-Mobile |
| Cingular | US Cellular |
| Metro PCS | Verizon |
| Rogers (Canada) | Virgin Mobile (US and Canada) |
ExtremeAnalytics Requirements
To use an ExtremeSwitching X440-G2 switch as an Application Telemetry source for ExtremeAnalytics, install firmware version 22.4.1.4-patch2-5 or higher.
- Extreme Portal
- Search the GTAC (Global Technical Assistance Center) knowledge base, manage support cases and service contracts, download software, and obtain product licensing, training, and certifications.
- The Hub
- Connect with other Extreme customers, ask or answer questions, and share ideas and feedback. This community is monitored by Extreme Networks employees, but is not intended to replace specific guidance from GTAC.
- GTAC
- For immediate support, call 1-800-998-2408 (toll-free in U.S. and Canada) or 1-603-952-5000.
Before contacting Extreme Networks for technical support, have the following information ready:
- Your Extreme Networks service contract number and/or serial numbers for all involved Extreme Networks products
- A description of the failure
- A description of any action already taken to resolve the problem
- A description of your network environment (such as layout, cable type, other relevant environmental information)
- Network load at the time of trouble (if known)
- The device history (for example, if you have returned the device before, or if this is a recurring problem)
- Any related Return Material Authorization (RMA) numbers